A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...



A South Korean game studio has reportedly rewarded all employees with a substantial bonus after selling over 5 mill...

Corsair’s ThermalProtect PCIe 5.1 cable redefines GPU power delivery with real-time thermal monitoring, combining 6...
A new AI model from NVIDIA unifies vision, audio, and language processing into one system, promising faster, more e...

Chinese smartphone manufacturers are rapidly adopting quad-curved display designs, mirroring Apple's iPhone 20, to...

The European Union’s new USB-C charging requirement for laptops under 100W signals a shift in hardware design, with...
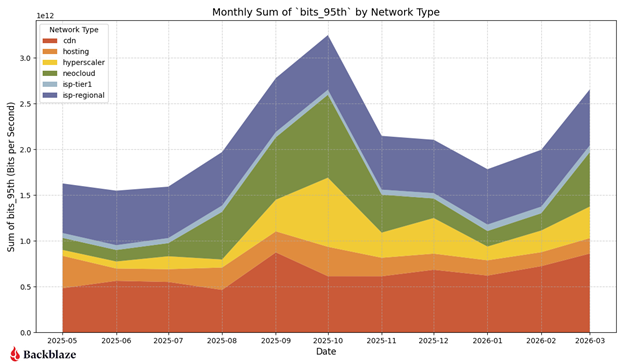
Q1 2026 network data from Backblaze indicates a cooling neocloud sector, rising CDN demand, and new geographic tren...

A 12-die hybrid bonded HBM stack has been verified by SK hynix, signaling a new phase in the high-bandwidth memory...

The new ROG Zephyrus Duo redefines dual-screen portability, pairing Intel Core Ultra 9 and NVIDIA RTX 5090 with fle...

The upcoming port of Final Fantasy VII Rebirth to the Nintendo Switch 2 is encountering significant performance iss...
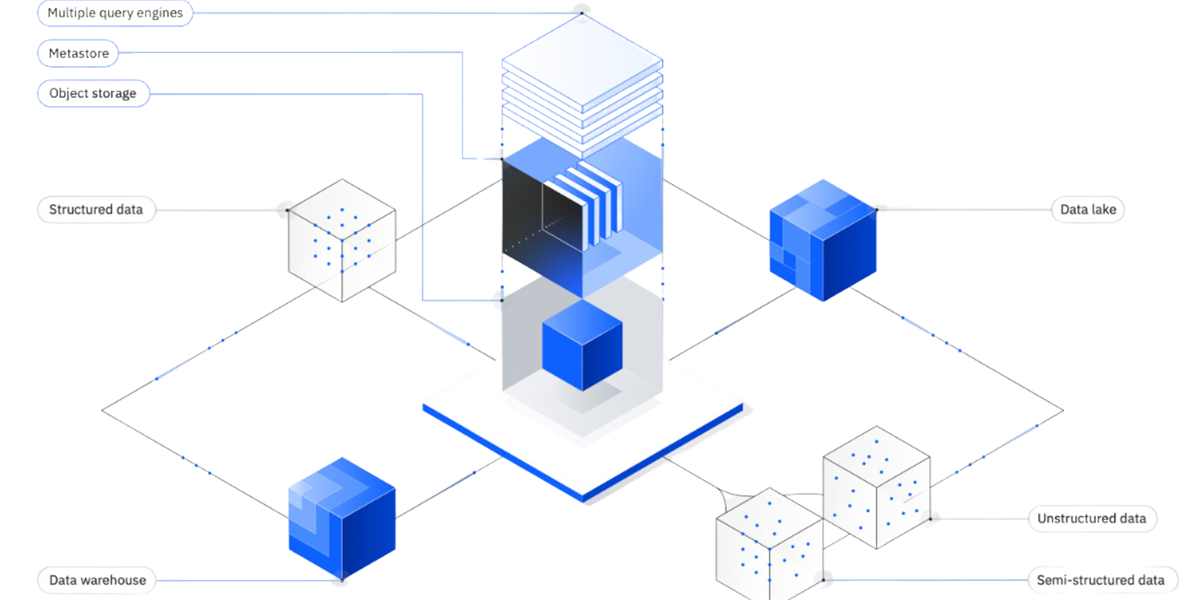
The latest collaboration between IBM and Google Cloud introduces tools designed to streamline enterprise AI trainin...