A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...


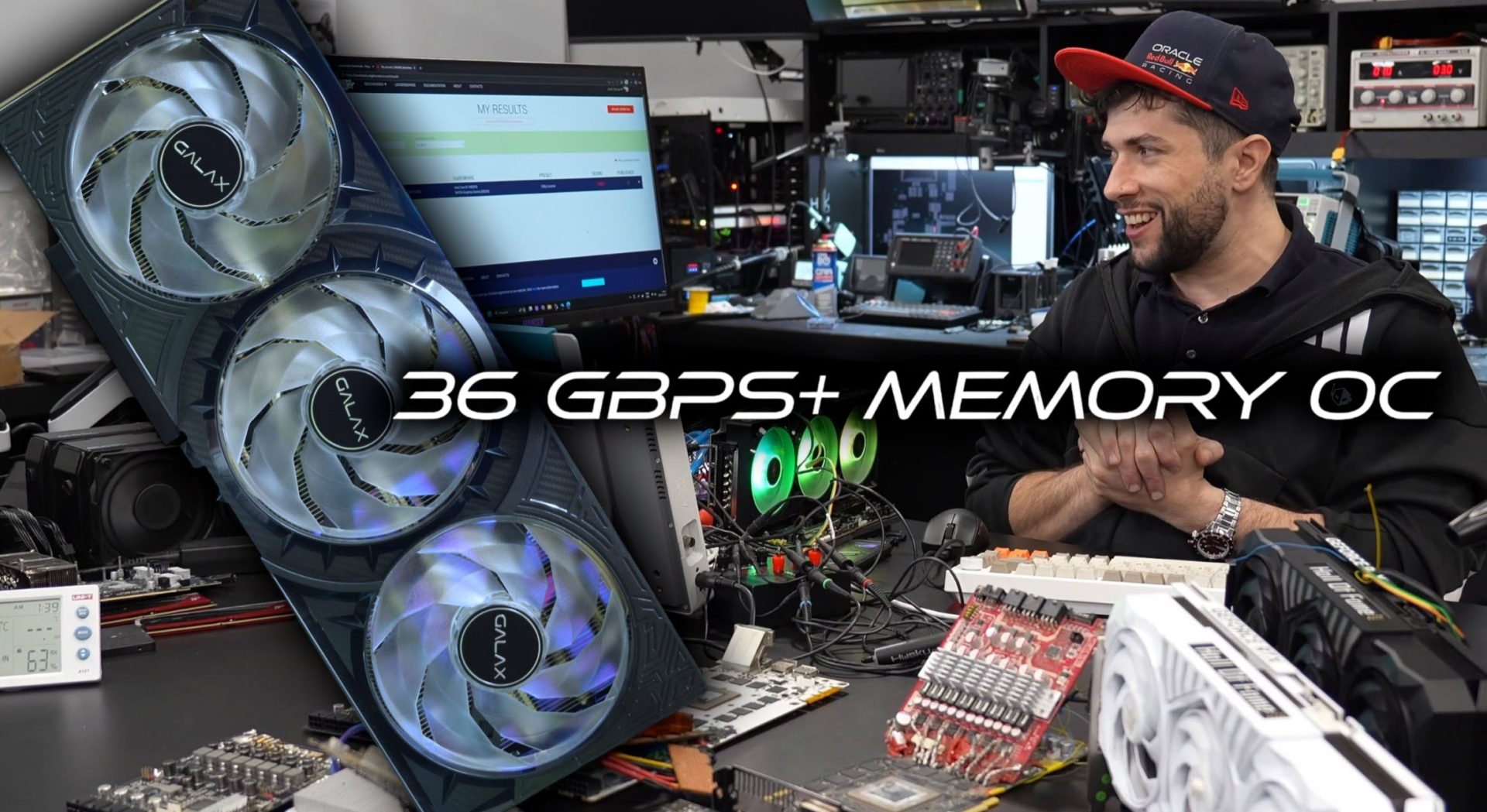
A new modding technique allows RTX 50 GPUs to exceed their official memory clock limits, achieving speeds up to 36...
The AMD Ryzen AI MAX+ 395 APU redefines compact workstations with its 16-core, 4nm design and RDNA 3.5 iGPU, offeri...

Two new Gigabyte Z890 motherboards drop just before Intel's Arrow Lake-S CPUs, offering Wi-Fi 7 and Bluetooth 5.4 w...

The AirPods 4 with Active Noise Cancellation have dropped to $119, offering a rare discount that makes them a compe...

The Logitech G PRO X Superlight 2 stands out with its ultra-light design, HERO 2 sensor, and optical switches for l...

The Galaxy S26 Ultra refines thermal management with advanced materials like graphite films and paste, while also s...

The new MacBook Neo offers a budget-friendly alternative with cost-cutting measures, but its limitations in perform...

The MacBook Neo’s 8GB unified memory is a defining feature of its mid-range positioning, but it also exposes a crit...

A 16GB kit of G.SKILL's AMD EXPO-optimized DDR5-6000 memory drops to $248, offering tight CL30 timings for Ryzen 70...
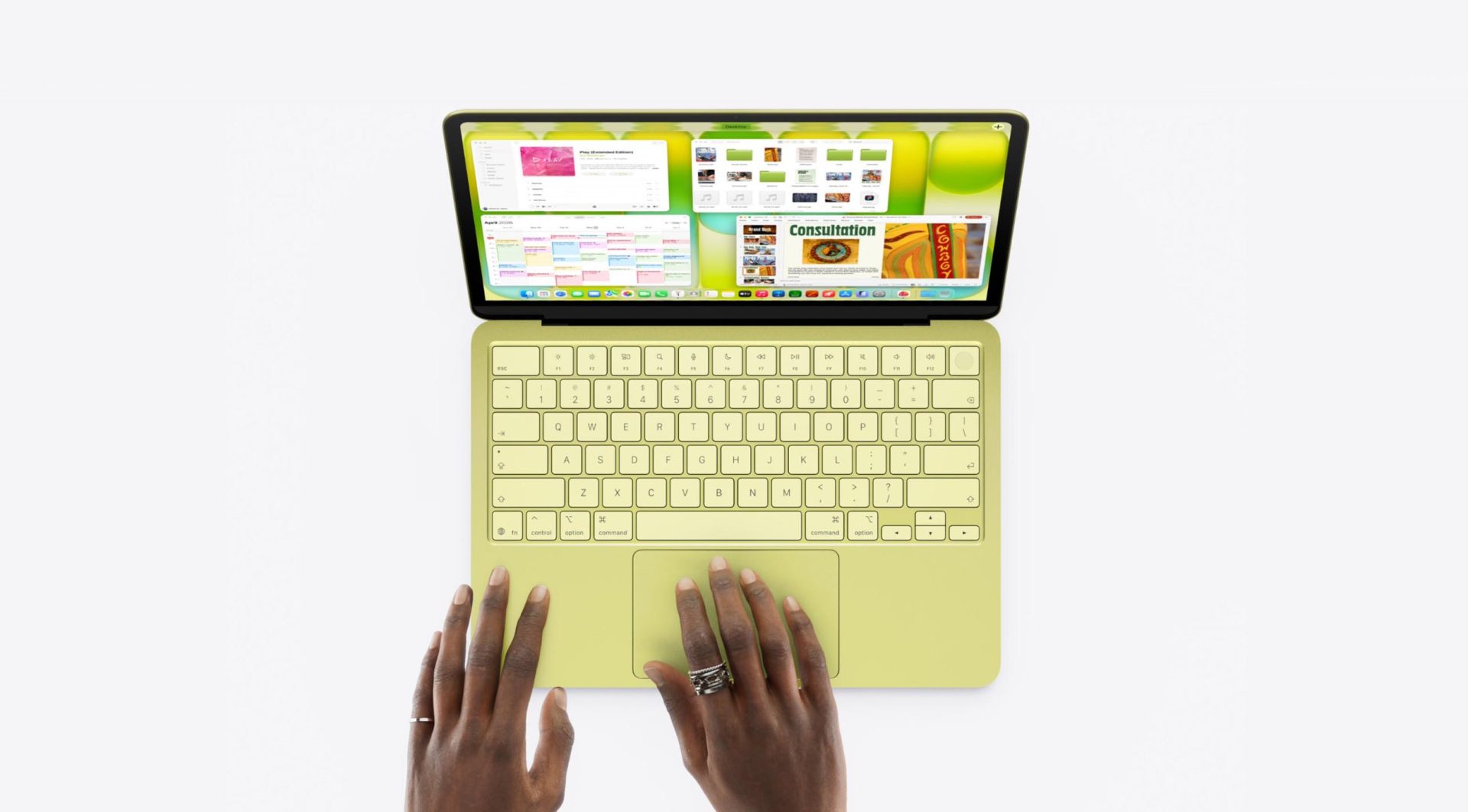
The new MacBook Neo delivers a significant performance boost over the five-year-old M1 MacBook Air, offering up to...