A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...


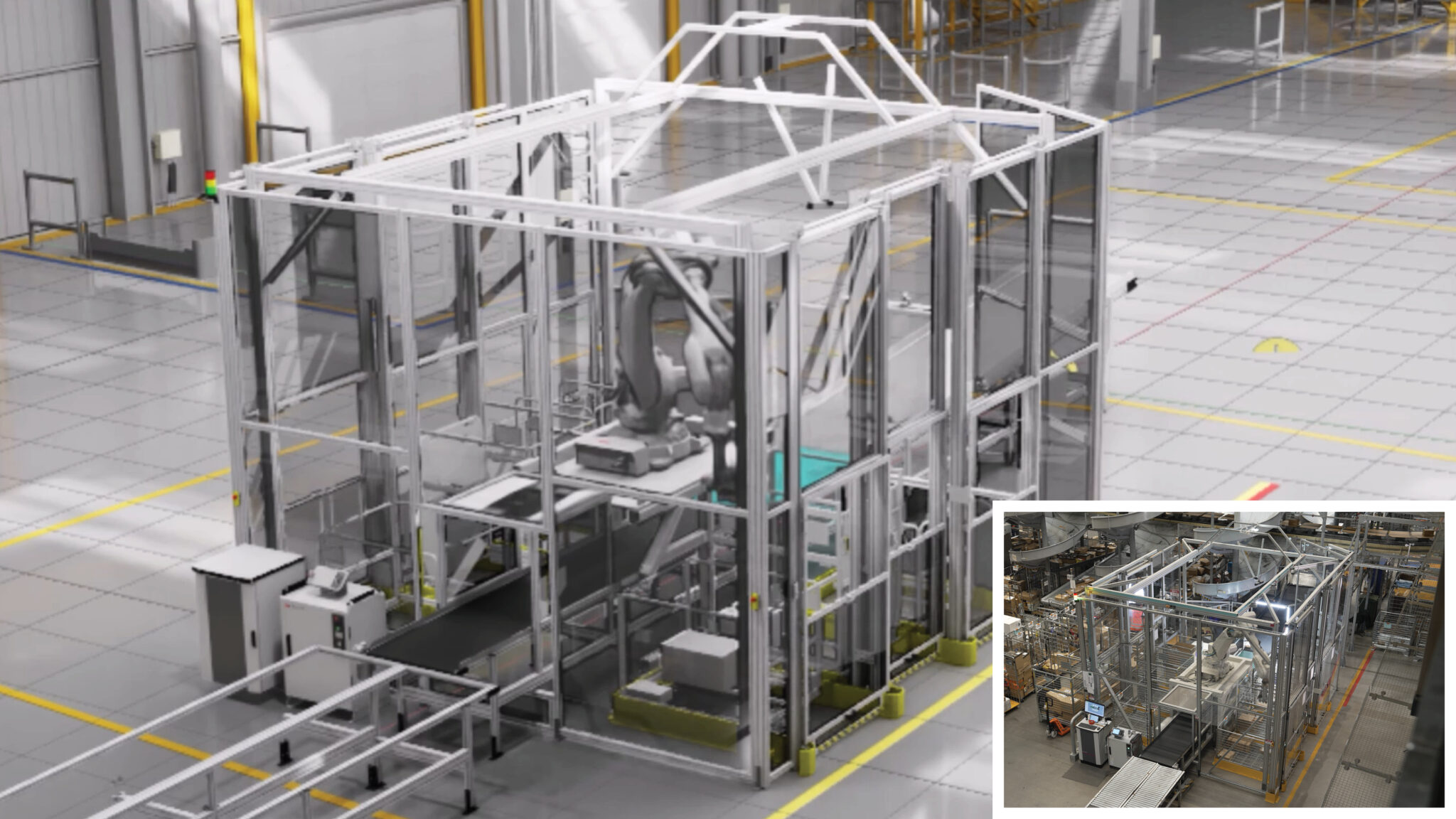
A new partnership between ABB Robotics and NVIDIA aims to integrate advanced simulation capabilities into industria...

A fresh action RPG from Bandai Namco Entertainment, set in the iconic world of Aincrad, launches on July 10, 2026....
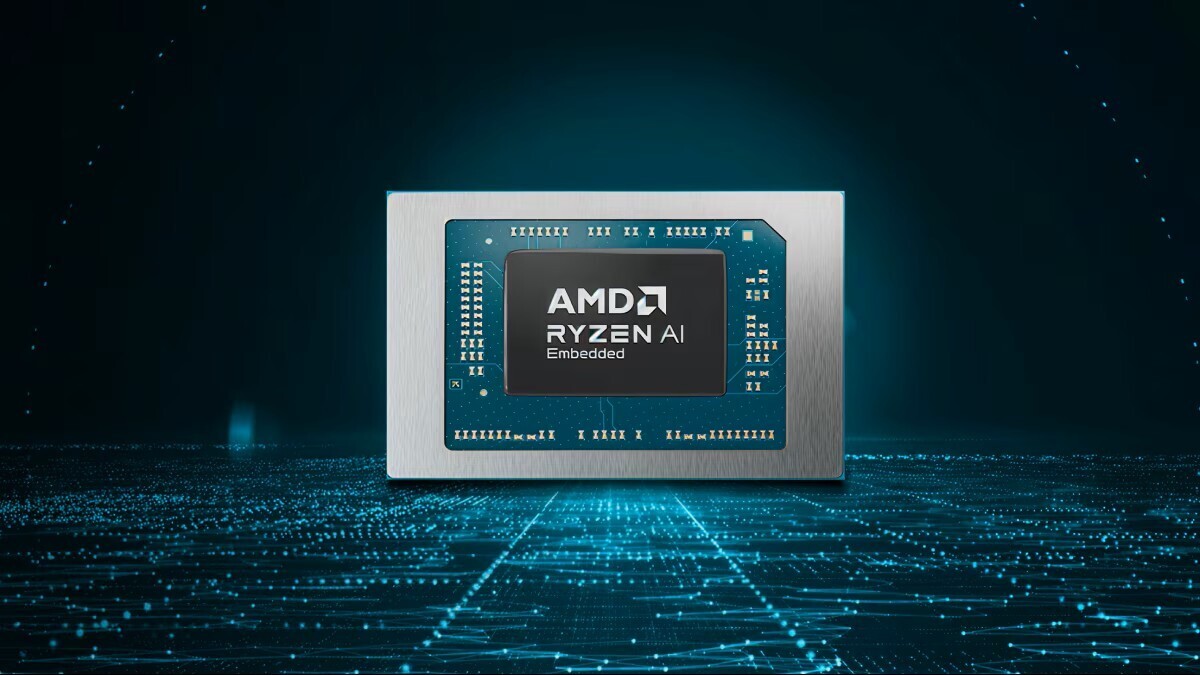
AMD has expanded its Ryzen AI Embedded P100 Series processor portfolio, introducing new processors that deliver sig...

Microsoft has pushed back the phase-out of its classic Outlook app by nearly a year, giving users more time before...
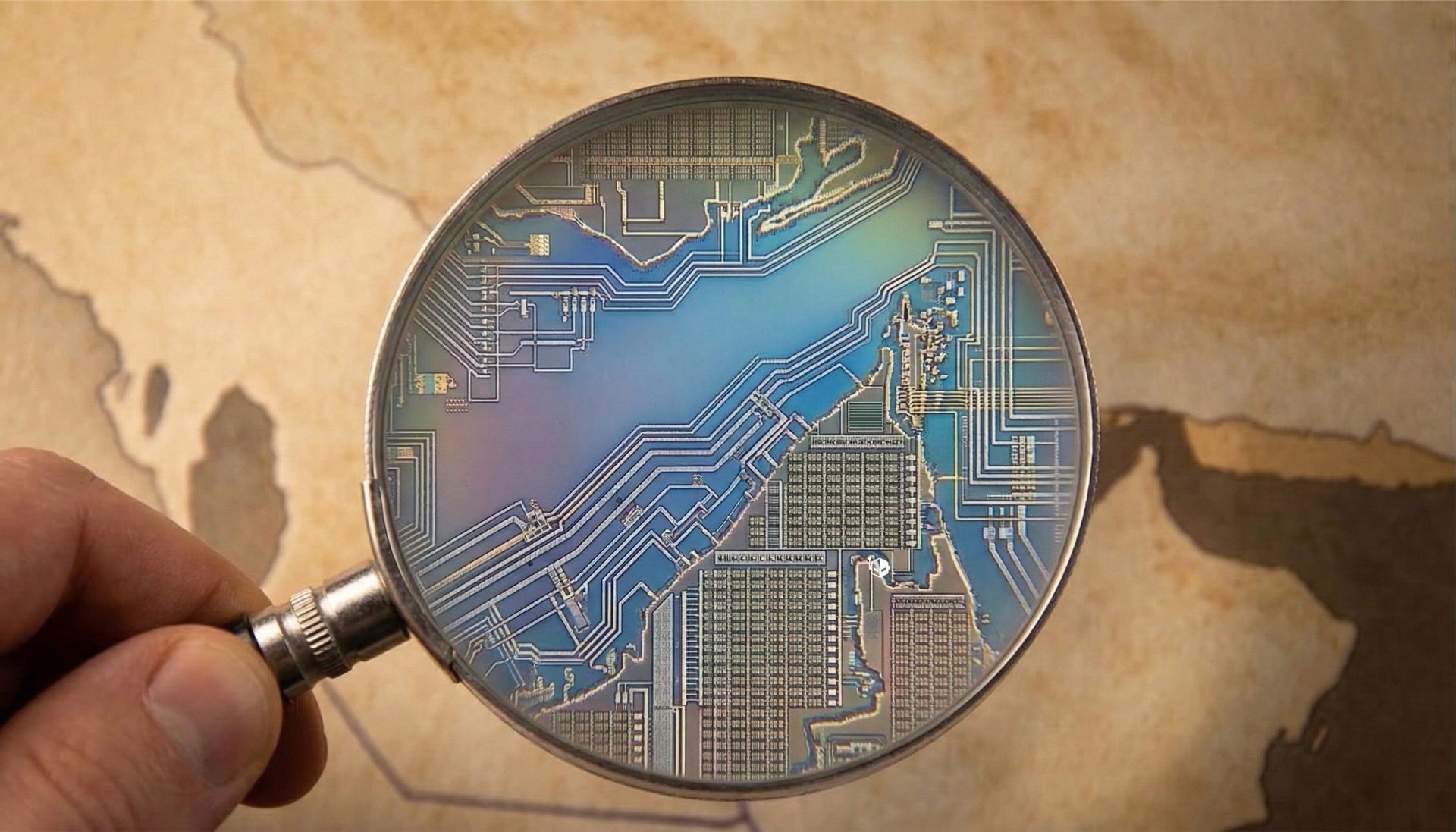
Geopolitical instability in the Middle East risks prolonging disruptions to global semiconductor and memory product...
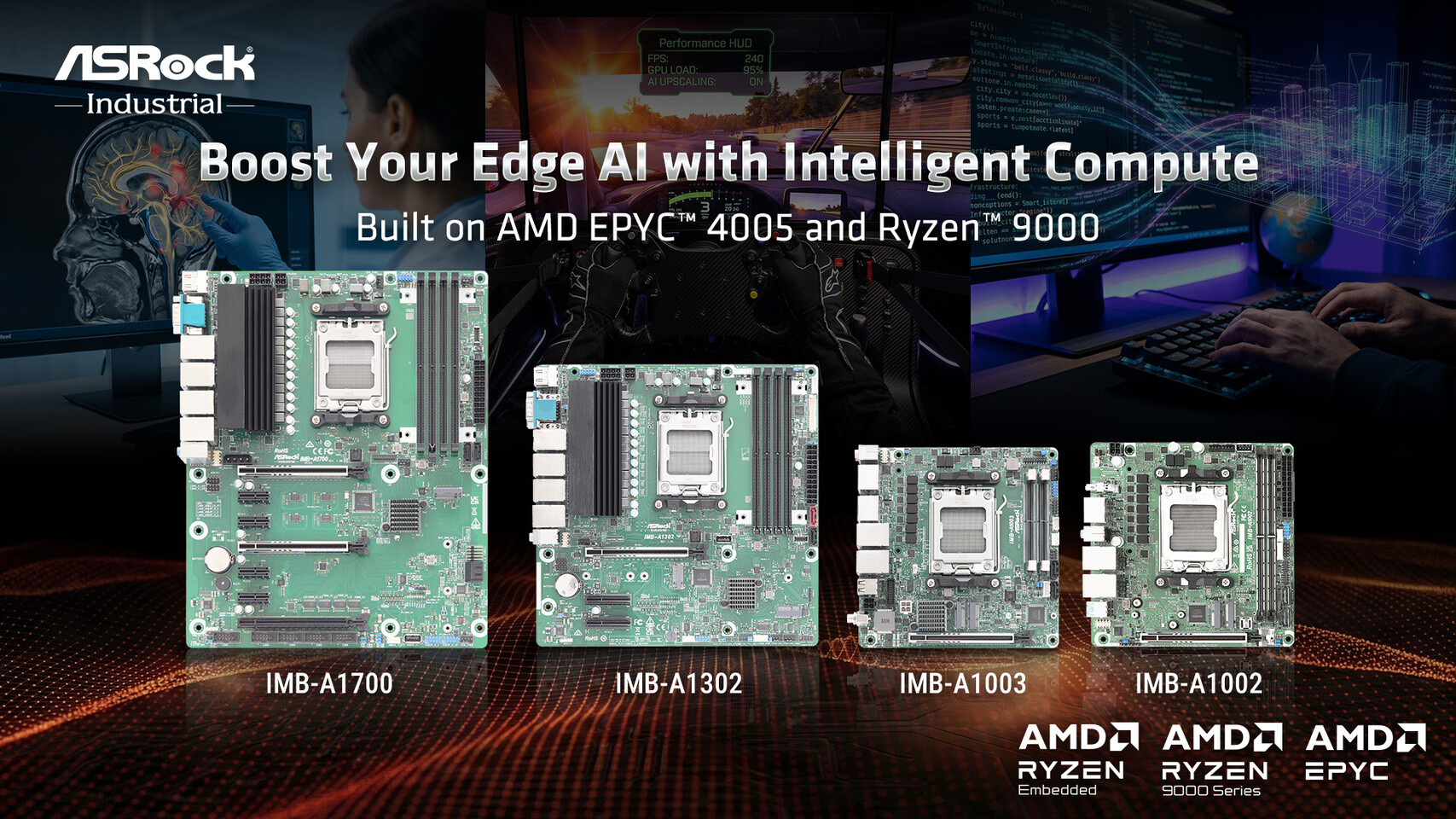
Four new ATX, microATX, and Mini-ITX boards support EPYC 4005 for edge servers and Ryzen 9000 for AI workloads, but...
A two-key shortcut can instantly clear Slack’s persistent unread message indicator, but this undocumented workaroun...

A new mini PC from AceMagic blends nostalgic Nintendo-inspired aesthetics with powerful specs, including a Ryzen AI...

A new benchmark reveals the Intel Core Ultra 5 250K Plus delivers a nearly 6% multi-threaded performance boost, out...

A new Lovecraftian survival game from Nacon will launch on PC, PS5, and Xbox Series in July 2026, promising intense...