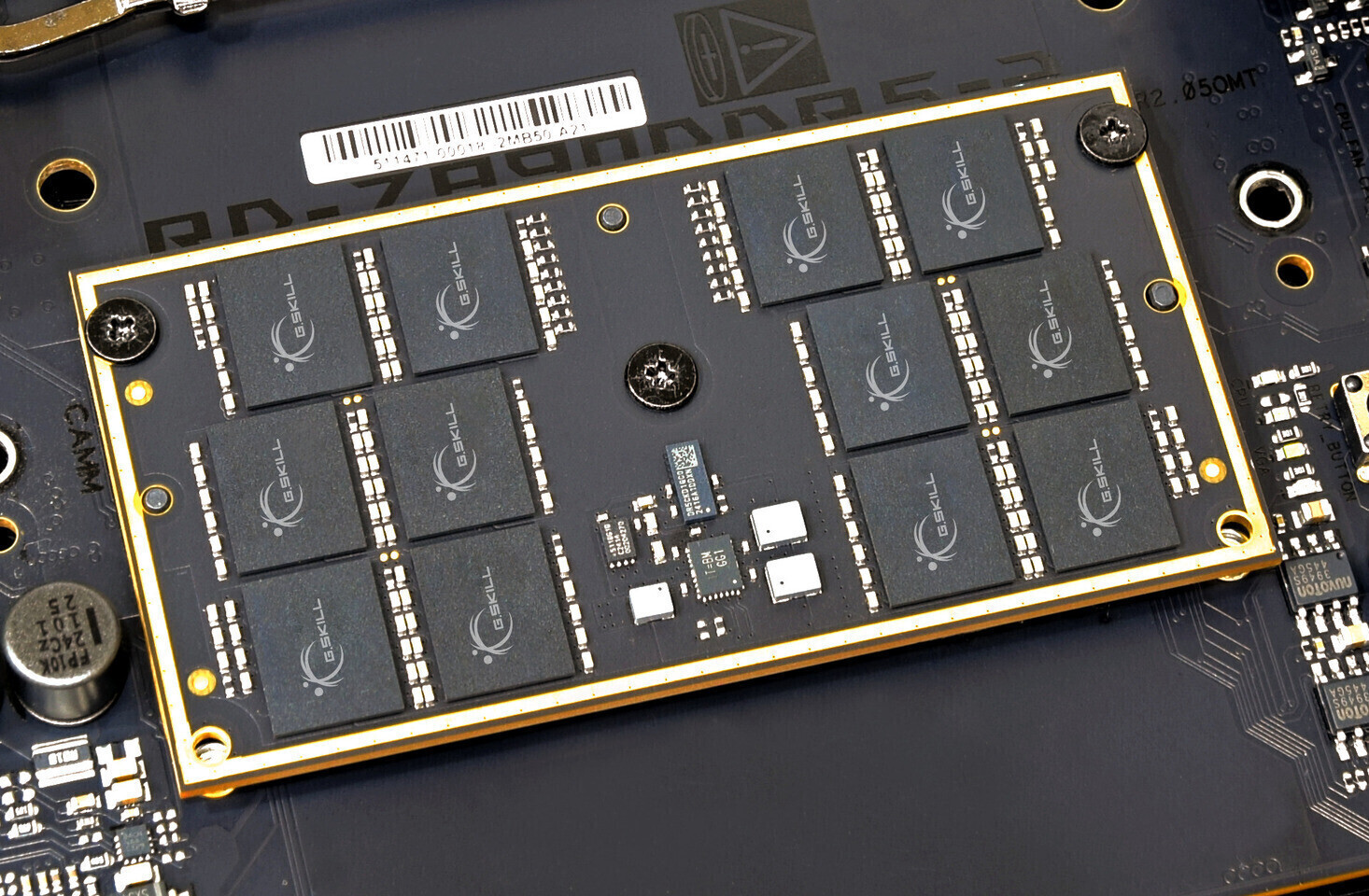
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...








Synology has achieved the rigorous ISO/IEC 27001:2022 certification, reinforcing its commitment to enterprise-grade...

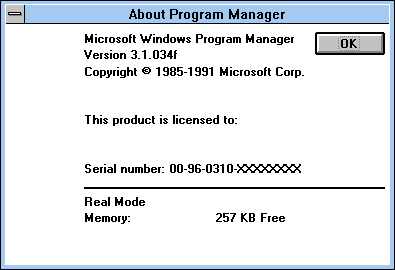
A new horror-adventure game from the creators of *Signalis* forces players to dig through a 1990s-inspired PC like...

The 24G4ZR and 27G4ZR bring esports-grade performance to budget gamers with 0.3 ms MPRT and overclocked 260 Hz refr...

Just weeks after its full launch, Riot Games has halved the 2XKO development team, signaling deep concerns over pla...

A sophisticated phishing campaign leverages deepfake CEOs, fake Zoom calls, and malicious 'troubleshooting' tools t...

Logitech’s new G Pro X2 Superstrike leverages its Haptic Inductive Trigger System (HITS)—a technology so transforma...

Edmund McMillen’s *Mewgenics* isn’t just a game with a long completion time—it’s a carefully constructed experience...

A decade after *The Witcher 3: Wild Hunt* redefined RPG storytelling, a confirmed DLC in development could upend ho...

The 24G4ZR and 27G4ZR deliver 0.3ms MPRT and overclocked refresh rates at prices starting under $150, challenging t...

Acer’s latest business laptop may not turn heads with its design, but under the hood, it delivers performance and e...