A new high availability architecture combines Scality's storage expertise with Veeam's backup solutions, promising enterprise-grade resilience without the complexity. IT teams must weigh performance claims agai...





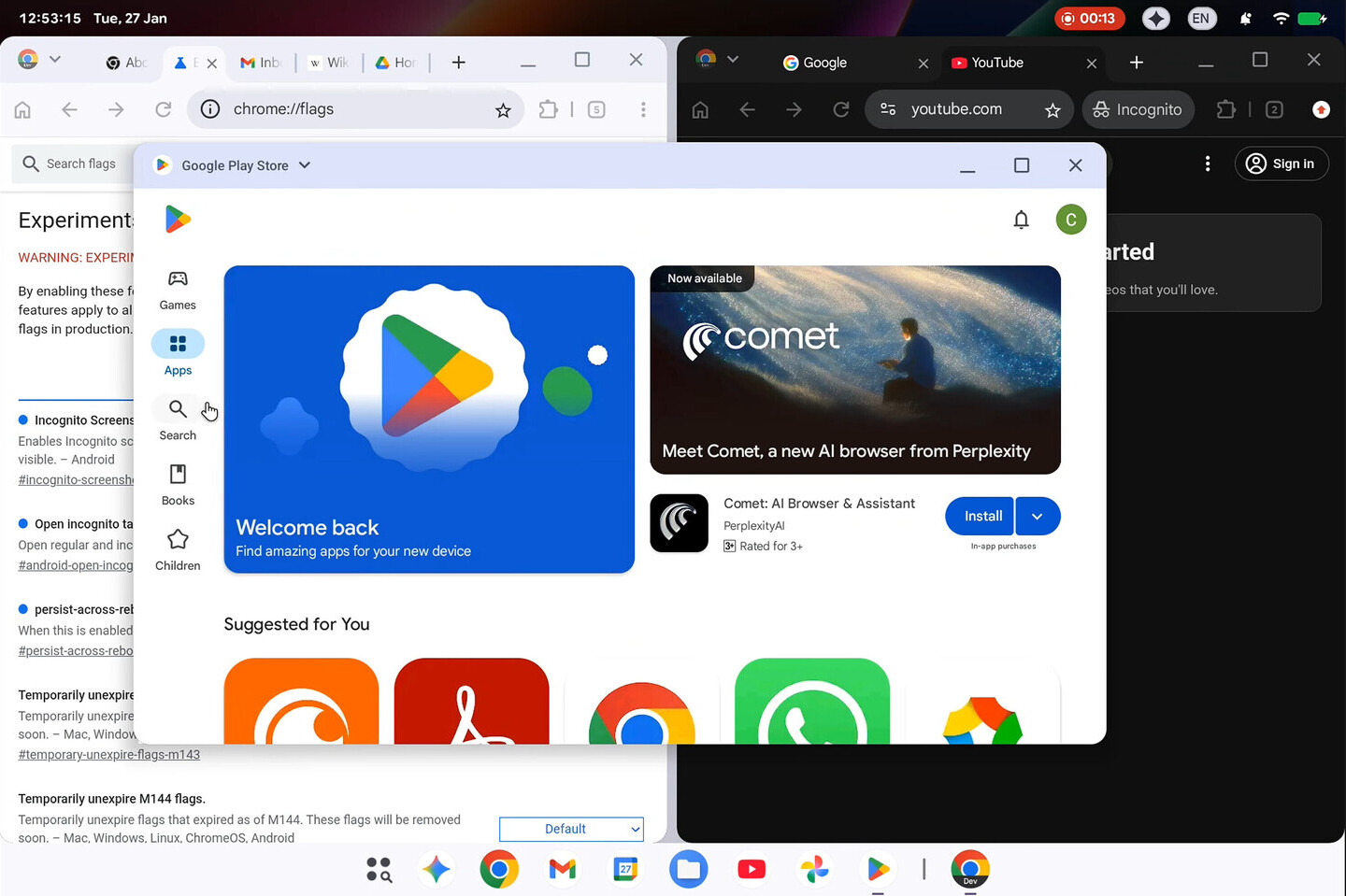
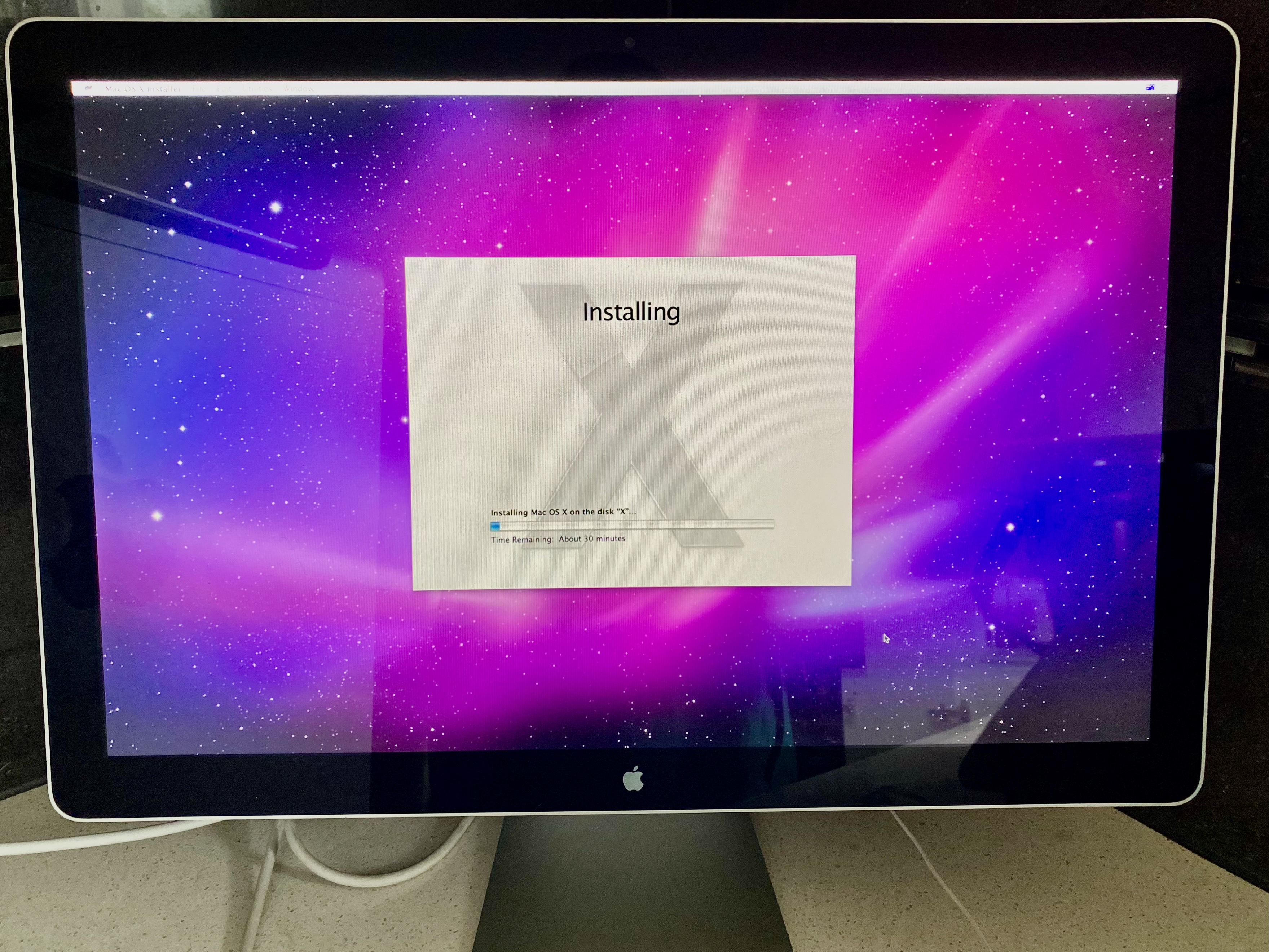
A newly leaked build of Google’s upcoming Aluminium OS reveals a desktop-focused Android variant running on Intel’s...

Blizzard’s three-part narrative arc promises bold storytelling, but players should brace for permanent character de...
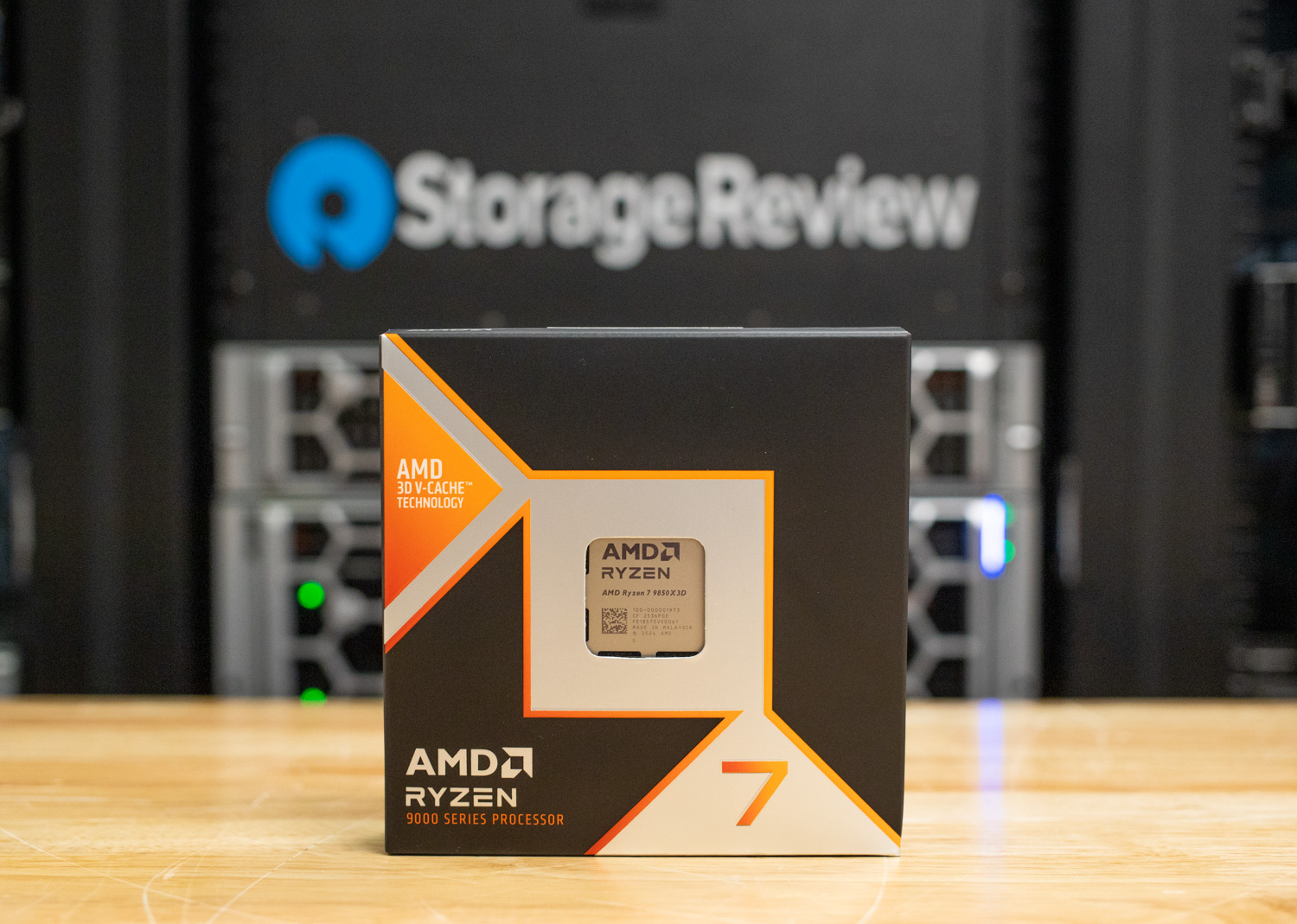
The Ryzen 7 9850X3D refines AMD’s X3D formula with higher clocks and architectural tweaks, offering modest but cons...

The new ZenBook Duo isn’t just a laptop—it’s a **dual-screen powerhouse** with Intel’s Core Ultra 7 chip, a **99Wh...

Nerial and Devolver Digital unveil Reigns: The Witcher, a narrative-driven twist on *The Witcher* series where play...

Kyle Hanagami’s career—from viral dance videos to collaborations with BLACKPINK and Mean Girls—has been shaped by F...
A decade ago, Western Sugar migrated to SAP S/4HANA Cloud Public Edition to escape a legacy ERP nightmare. Today, t...

The new InfinityBook Max 15 combines Intel’s Core Ultra 7 255H processor with NVIDIA’s GeForce RTX 5060/5070 GPUs,...

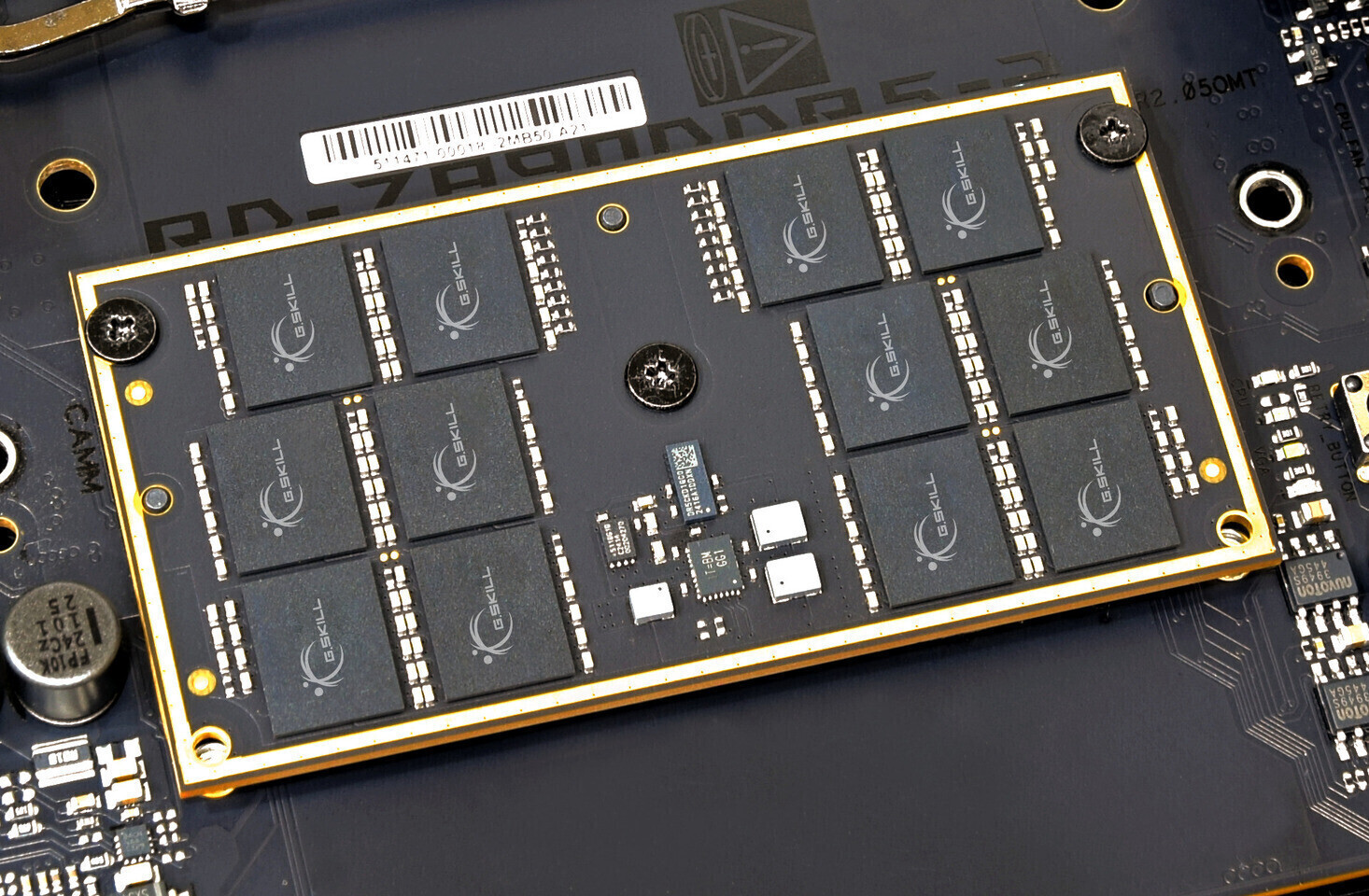
Graphics card production faces existential risks as memory shortages cripple supply chains, with one major manufact...

A compact USB-C or USB-A card reader that supports both SD and microSD formats is now available for just $9—half it...