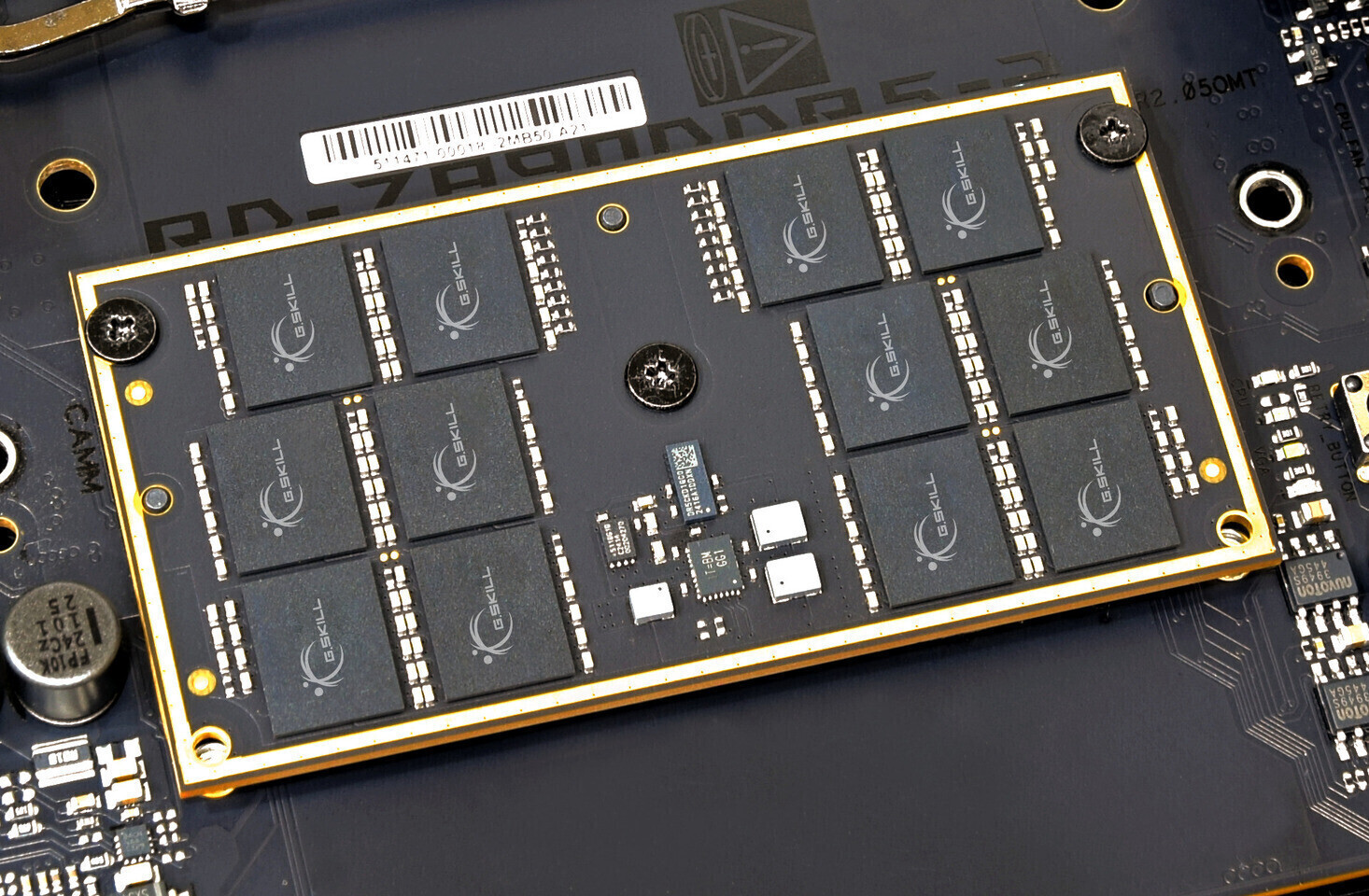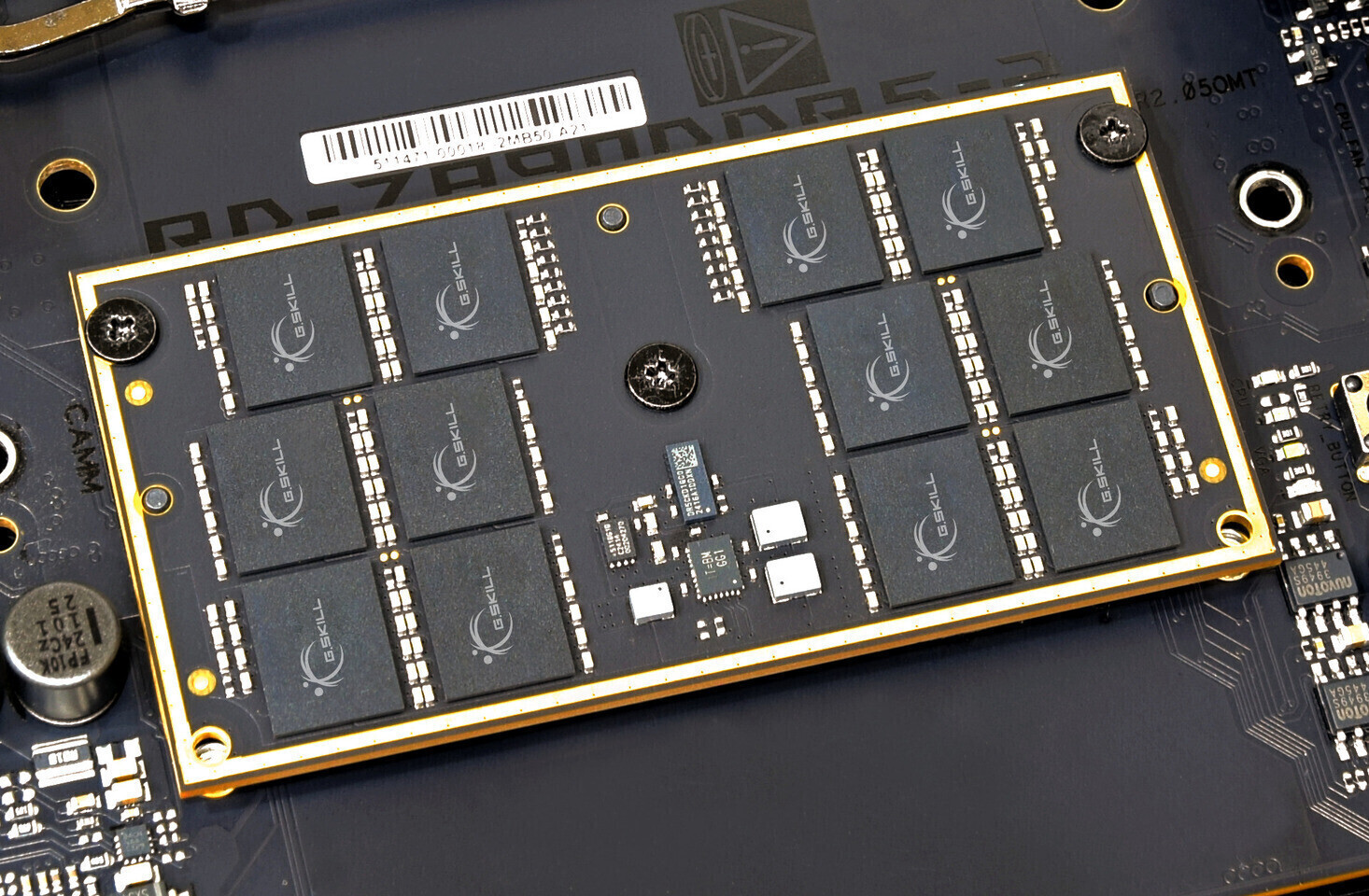
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...




iOS 27 is set to introduce a multi-agent Siri system, blending multiple AI personas for complex tasks. This shift c...

Bungie’s Marathon has sold an estimated 1.2 million units across PC, PlayStation 5, and Xbox Series platforms since...

On April 29, Rockstar’s 'Neverness to Everness' launches across PC, PlayStation 5, and mobile, introducing a new be...

The highly anticipated 3D remake of the classic precision platformer Super Meat Boy is set to launch on March 31, b...

Players can now experience the zero-gravity challenges and tactical combat of The Expanse: Osiris Reborn during a c...

The RTX 5090 is the latest in NVIDIA's high-end lineup, designed to handle the demands of AI-driven workloads. Howe...

Five new games have joined the cloud library, including an arcade racer built for RTX 5080 and a major update to a...

A new sci-fi tactical RPG developed by former Blizzard veterans is set to launch on PC, blending turn-based strateg...

A new Xbox exclusive merges Lovecraftian dread with retro VHS aesthetics, promising a first-person shooter that red...

While Google's new TurboQuant architecture delivers measurable performance improvements, real-world deployment reve...