The new RTX 50 series GPUs promise significant efficiency gains, but their higher thermal output may challenge small businesses to rethink cooling strategies without compromising performance.





A new analysis suggests Apple’s move toward unified memory design will accelerate its growth, potentially making it...
NVIDIA has taken a significant step forward in AI development by optimizing its software stack for the newly releas...

A new Office 2024 suite is now available as a one-time purchase for $114, including comprehensive training courses....
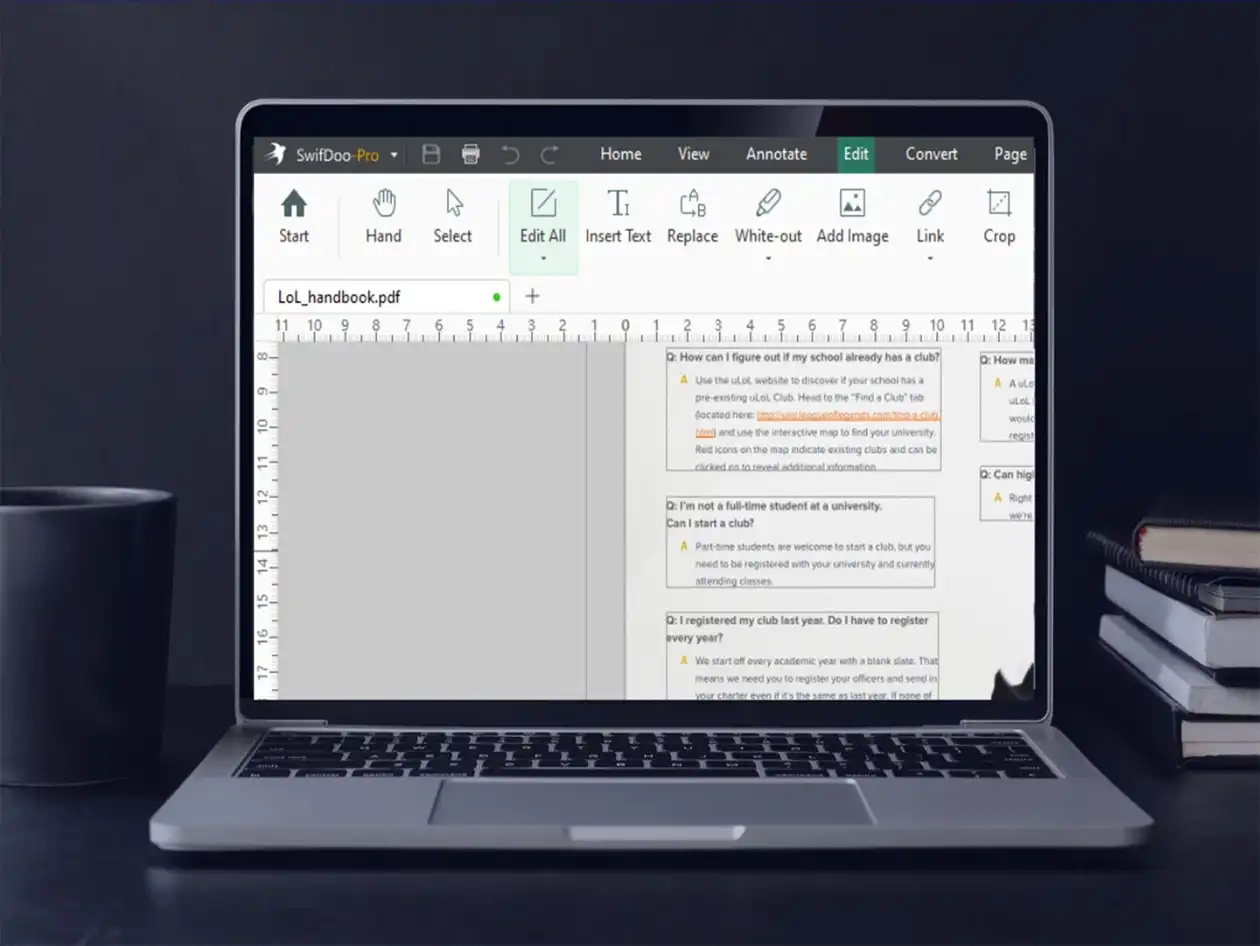
A one-time purchase now delivers enterprise-level PDF processing—editing, merging, compression, and conversion—at a...
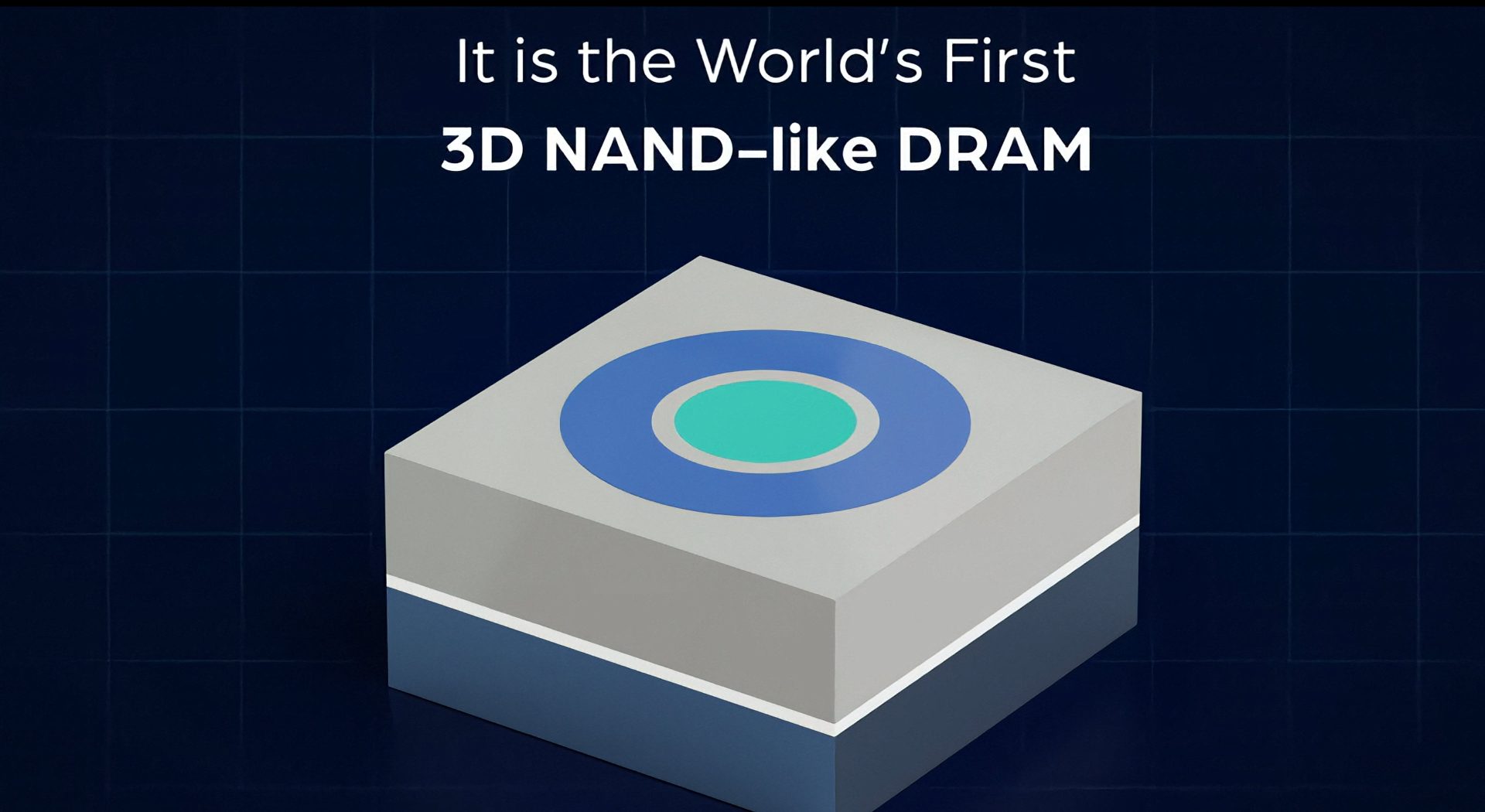
A proof-of-concept for 3D X-DRAM suggests it could deliver 10 times the density of traditional DRAM, offering a hig...
A man was arrested after selling a stolen Mac mini, leaving behind digital fingerprints that traced back to his own...

A brief but revealing Steam page leak has set the stage for Star Wars Galactic Racer, with an anticipated launch wi...

A potential 36-day shutdown at Samsung’s DRAM plants could trigger a $20 billion financial blowout, deepening globa...

A leaked review offers a first look at Valve's new Steam Controller, revealing its $99 price tag and key performanc...
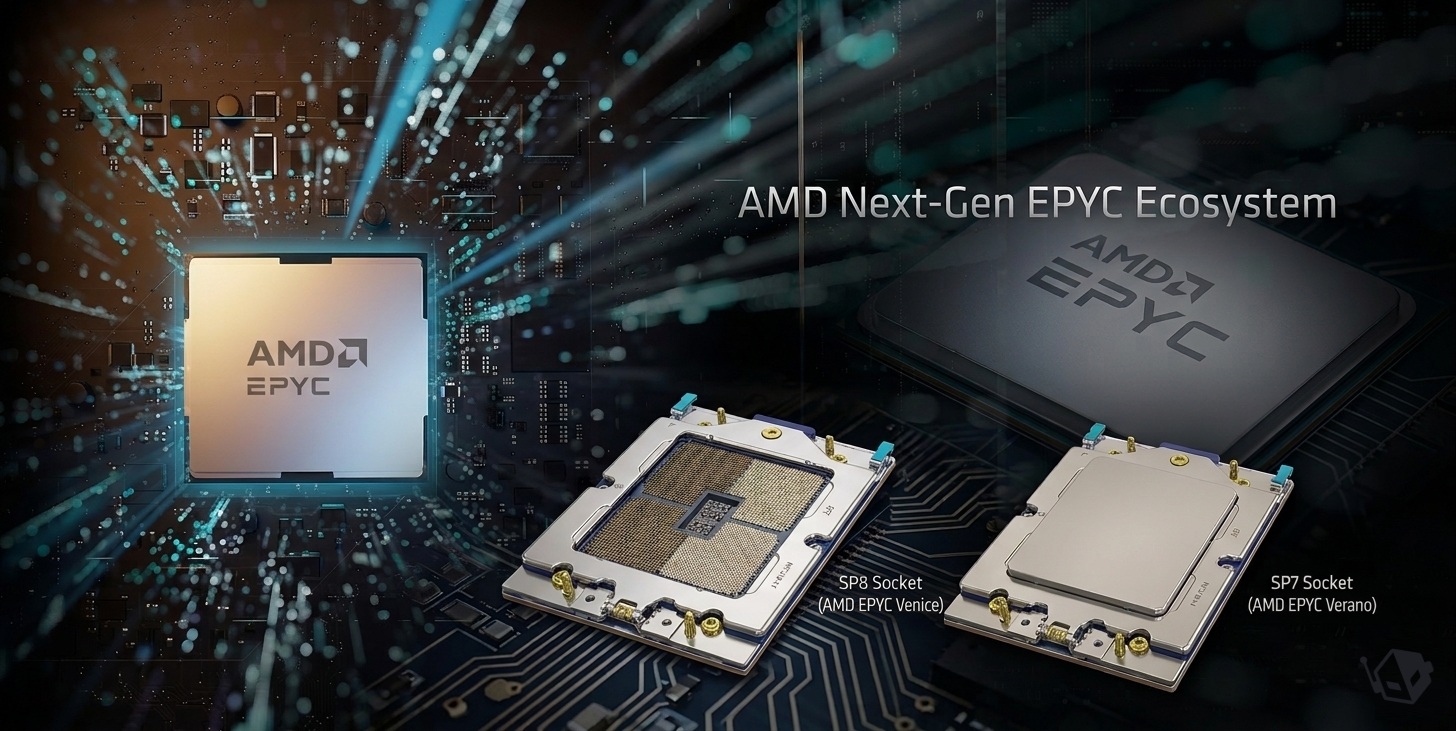
AMD’s Venice and Verano processors, paired with SP7 and SP8 sockets, mark a turning point in server design. The lar...