

Nintendo's upcoming console generation faces both excitement and uncertainty, with potential blockbuster titles on the horizon. While development is underway, industry analysts question whether the company can...





A brief but noticeable chat filter issue in Marathon caused 'Arc Raiders' to be censored, mirroring similar inciden...
Intel's semiconductor foundry operations will see a significant leadership change, with Naga Chandrasekaran steppin...

The iPhone 16 Pro Max is now available as Renewed Premium on Amazon, offering near-flagship performance at signific...

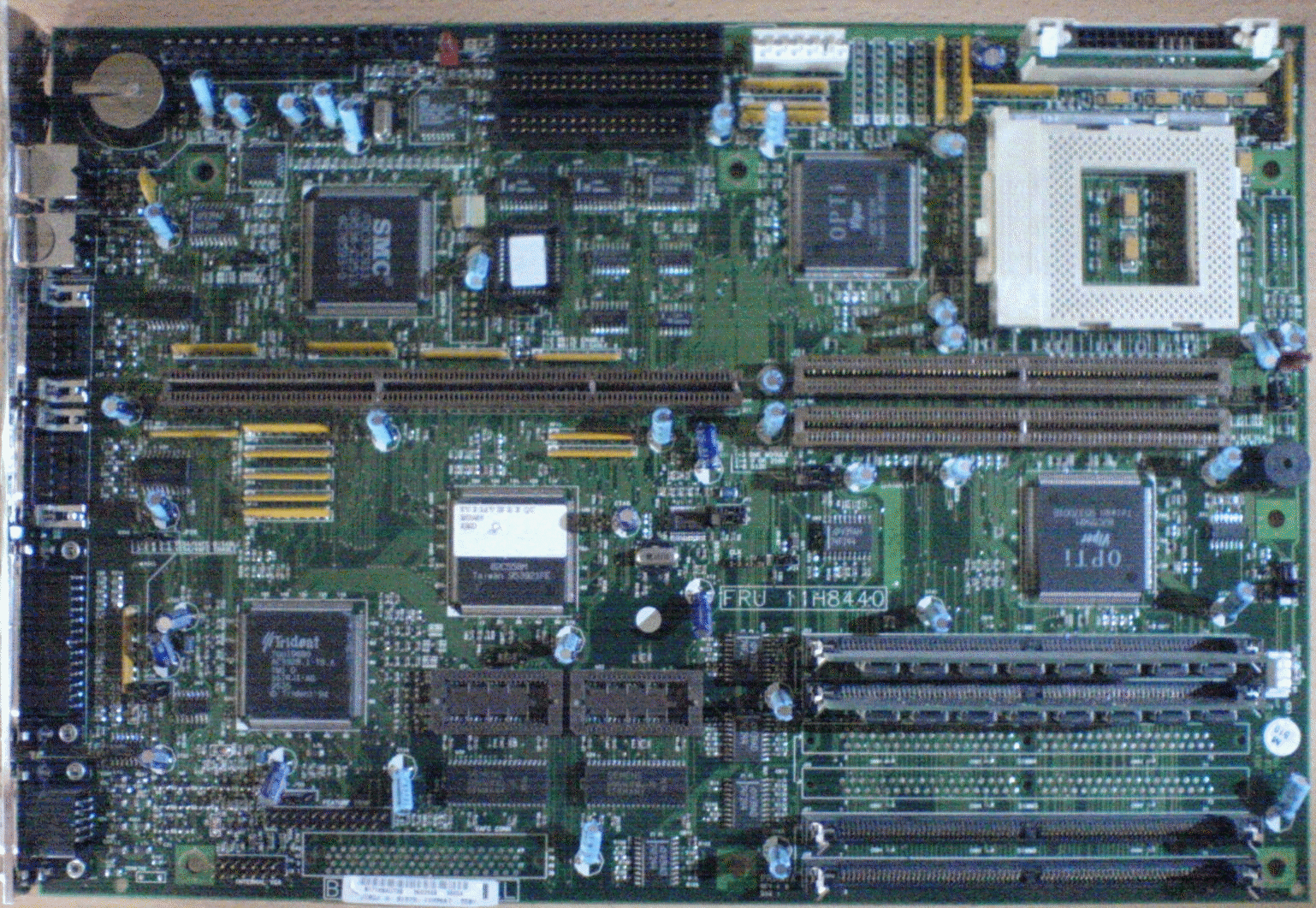
An unexpected warehouse mix-up led one buyer to receive ten DDR5 modules instead of the single kit they paid for, h...
Capcom's Umbrella Corporation has filed a fictional copyright lawsuit against Nissin Foods, claiming its Cup Noodle...

The upcoming dungeon brawler Awaysis reimagines the action RPG genre with a focus on physics-driven movement, blend...

Quantic Dream's Spellcasters Chronicles is now available in Early Access, inviting players to shape the game's futu...

Running With Scissors is set to debut its first spinoff title, 'Flesh & Wire,' a dark and violent return to the POS...

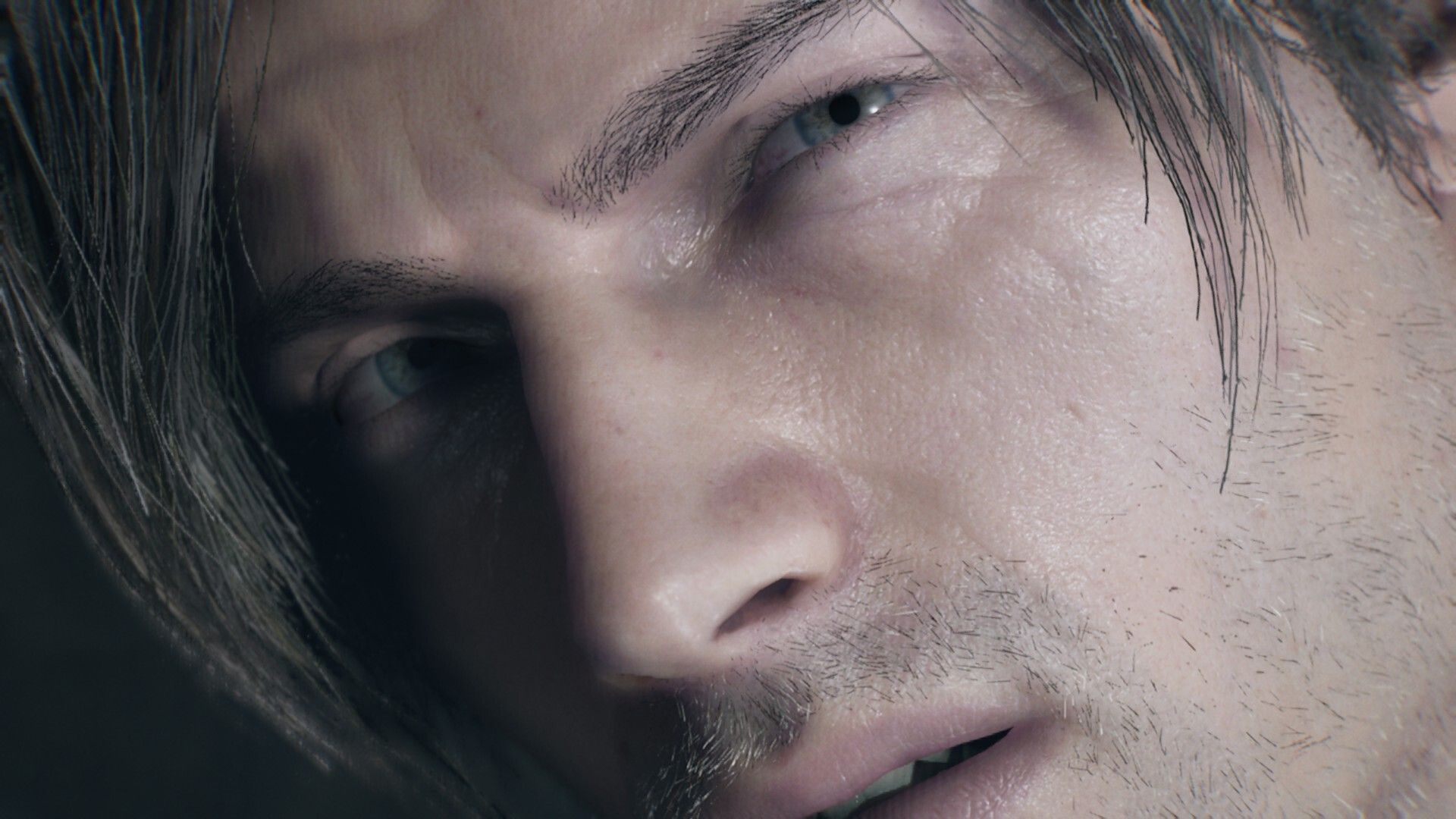
Earning the cat ears accessory in Resident Evil 4 Remake requires completing the game on Professional difficulty wi...

A recent patch for Alan Wake Remastered introduces HDR support, a new camera style mode, and several gameplay impro...





