

Nintendo's upcoming console generation faces both excitement and uncertainty, with potential blockbuster titles on the horizon. While development is underway, industry analysts question whether the company can...







The Meta Quest 3 introduces a 512 GB variant that doubles graphics performance, paired with a one-month Xbox Game P...

Two Hisense mini-LED TVs, including a 75-inch and an 85-inch model, have seen significant price reductions, making...

The GMKtec EVO-T2 redefines mini PC portability by leveraging Intel’s Panther Lake architecture to deliver desktop-...

A leaked report suggests a $699 PlayStation 5 could still emerge with the right financial support, though Sony appe...
A recent decline in DDR5 memory prices—estimated at around 10%—marks a pivotal moment in the market, suggesting a s...
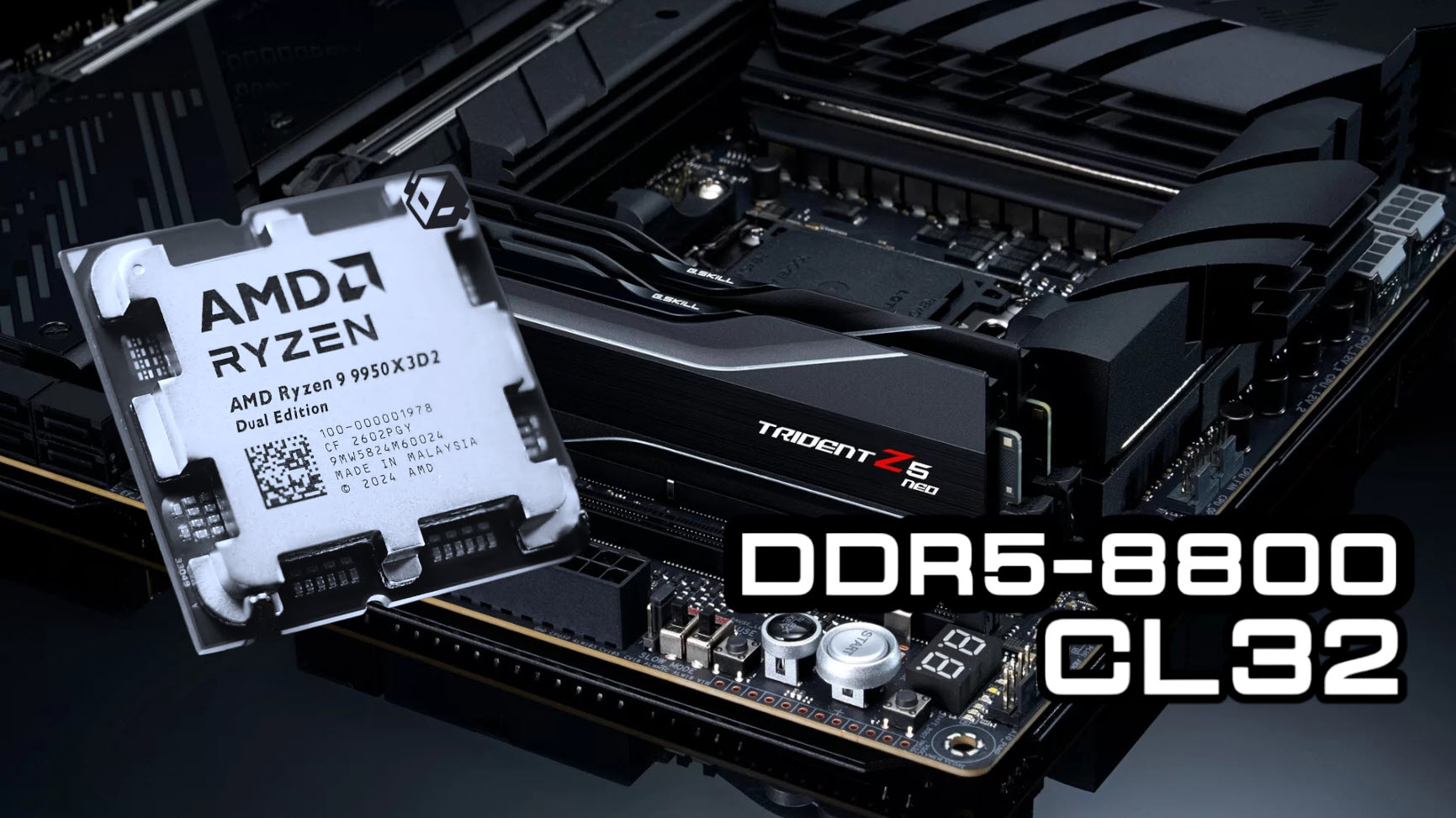
The ASUS ROG X870E APEX motherboard demonstrates impressive overclocking capabilities with DDR5-8800 memory on the...
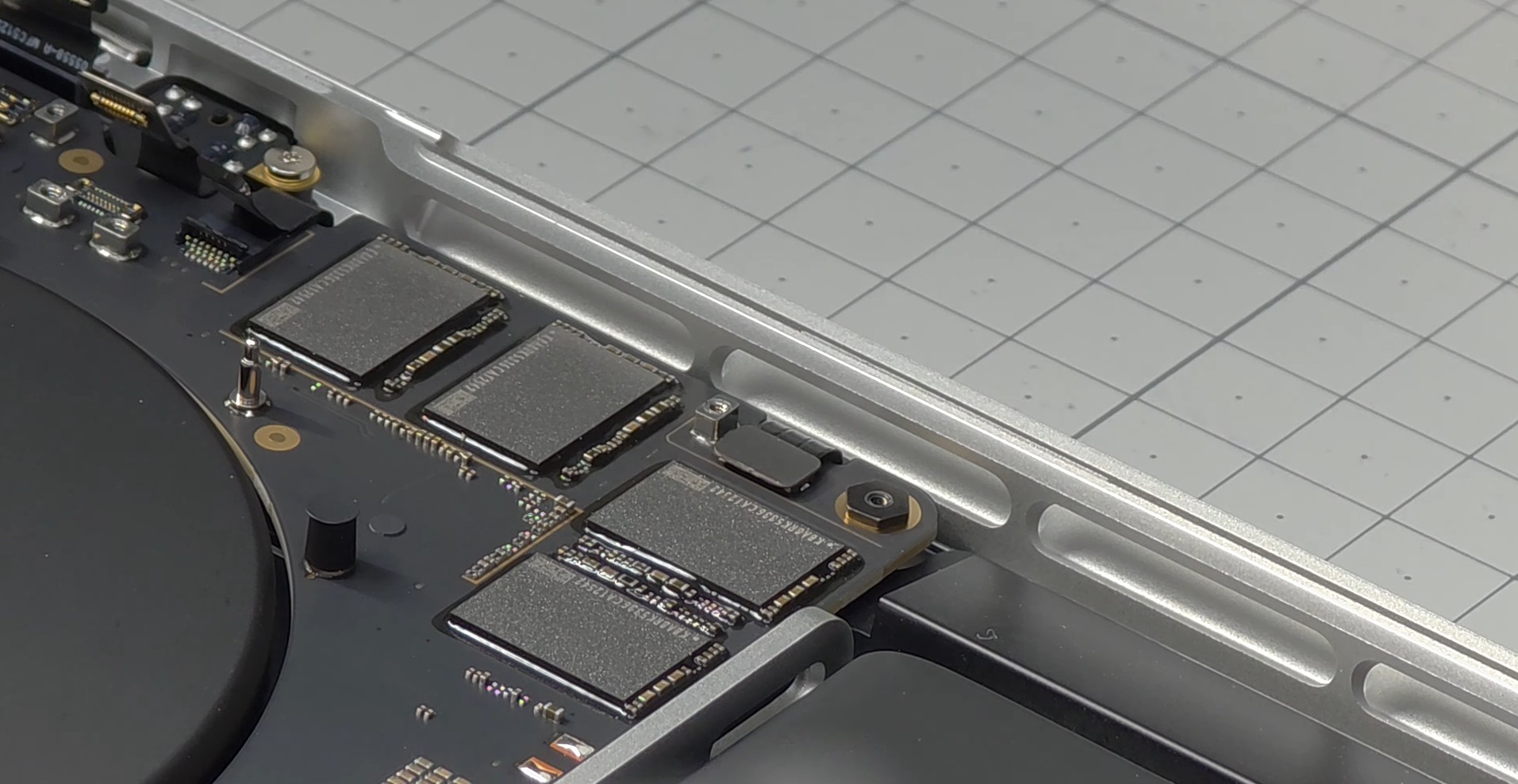
A user’s benchmarking session with the M5 Max MacBook Pro reveals extreme SSD temperature spikes during AI tasks, p...
The top-tier RDNA 4 GPU has dropped to $699 with bundled accessories, making it a rare opportunity for gamers to up...

A new CPU architecture arrives with a 16-core monster, but motherboards must evolve just as fast to support it. The...

Two new TP-Link Wi-Fi 7 routers deliver high speeds, low latency, and broad coverage at accessible prices, making t...





