

Nintendo's upcoming console generation faces both excitement and uncertainty, with potential blockbuster titles on the horizon. While development is underway, industry analysts question whether the company can...




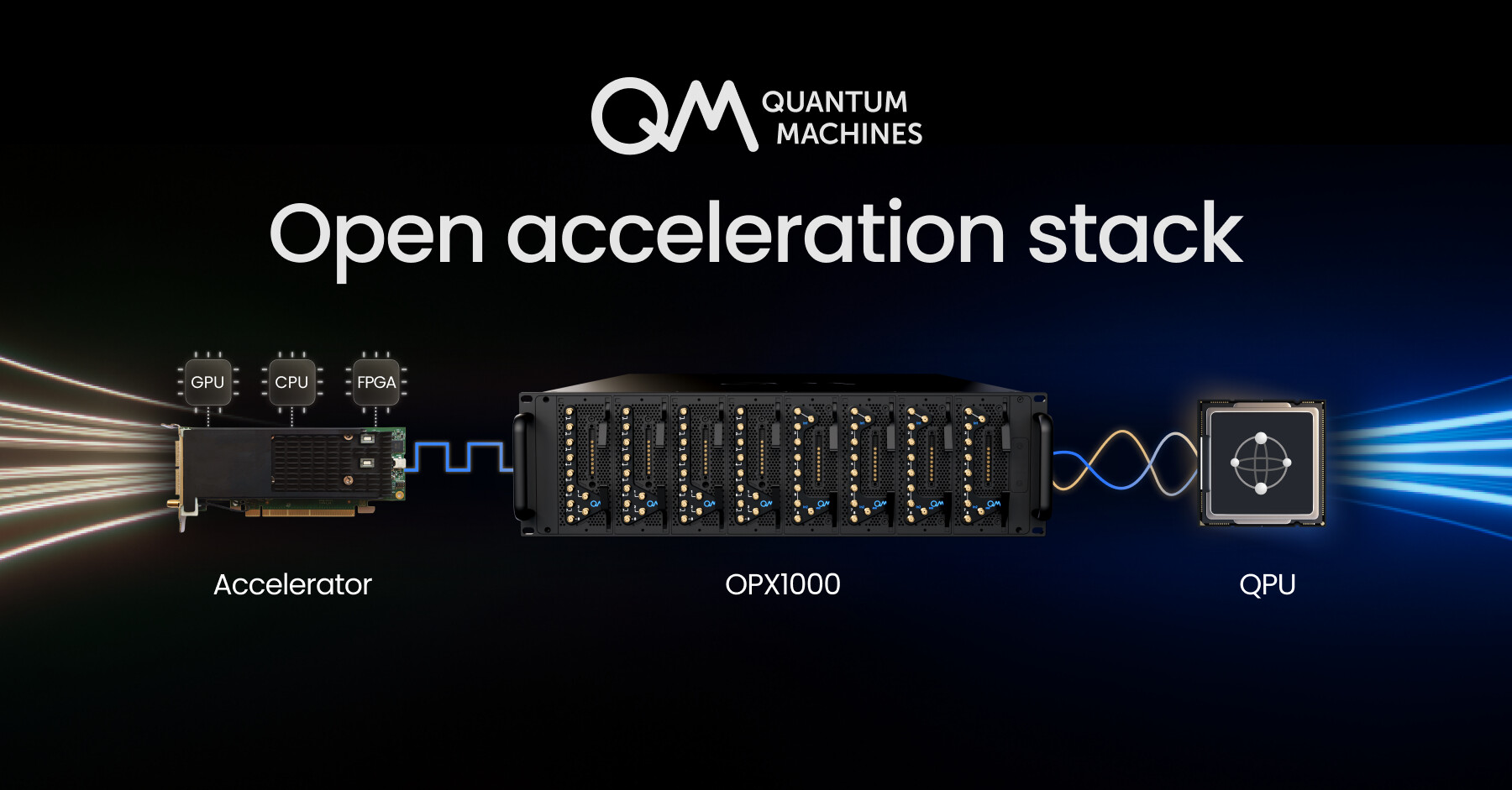
A new framework from Quantum Machines enables seamless integration between quantum processors and high-performance...
A new update to Microsoft's Windows PowerToys utility introduces three significant features: a quick file path copi...
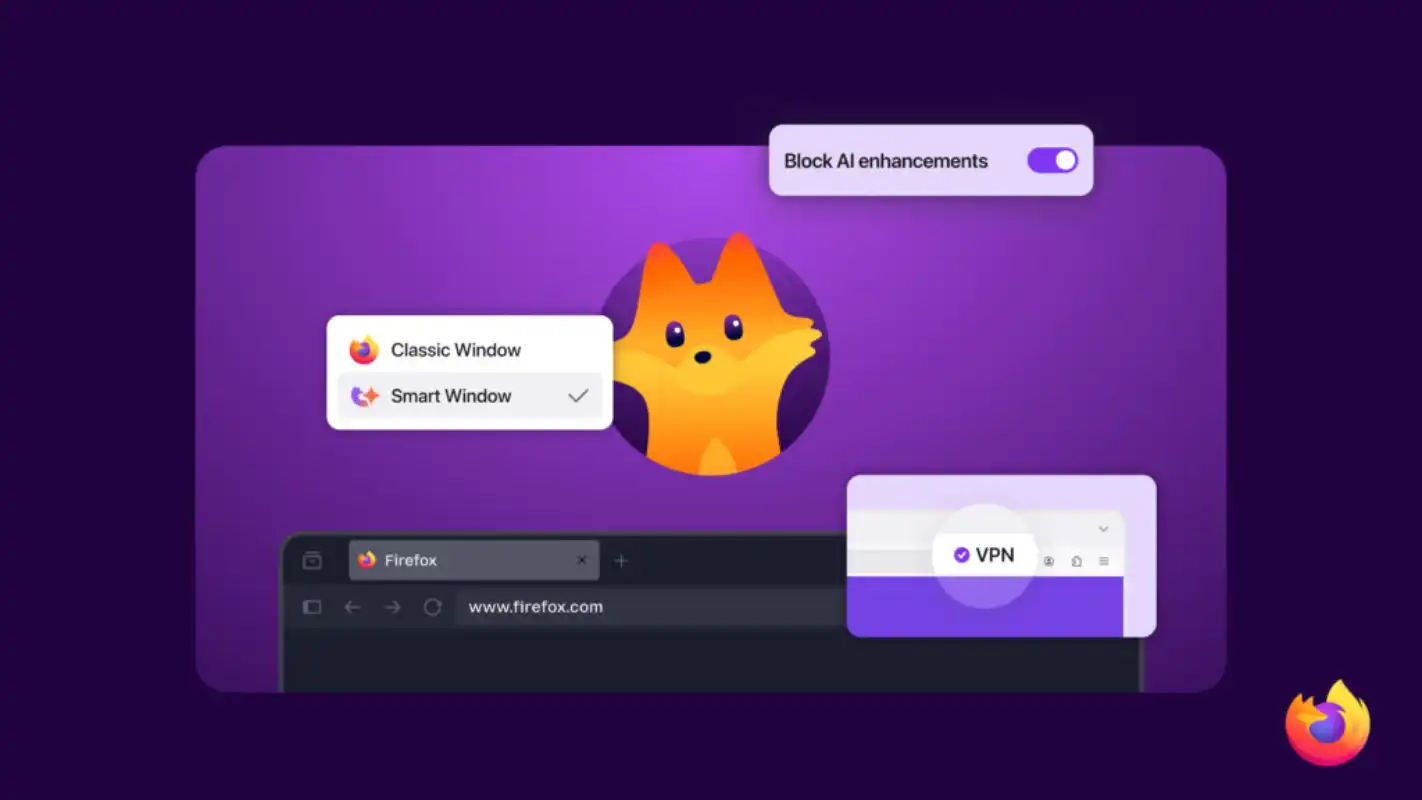
Mozilla’s Firefox is adding a free built-in VPN and multi-monitor split-view mode, giving users more control over p...

A new gameplay trailer for Saros offers a first look at how the game will utilize PS5 features, including fast load...
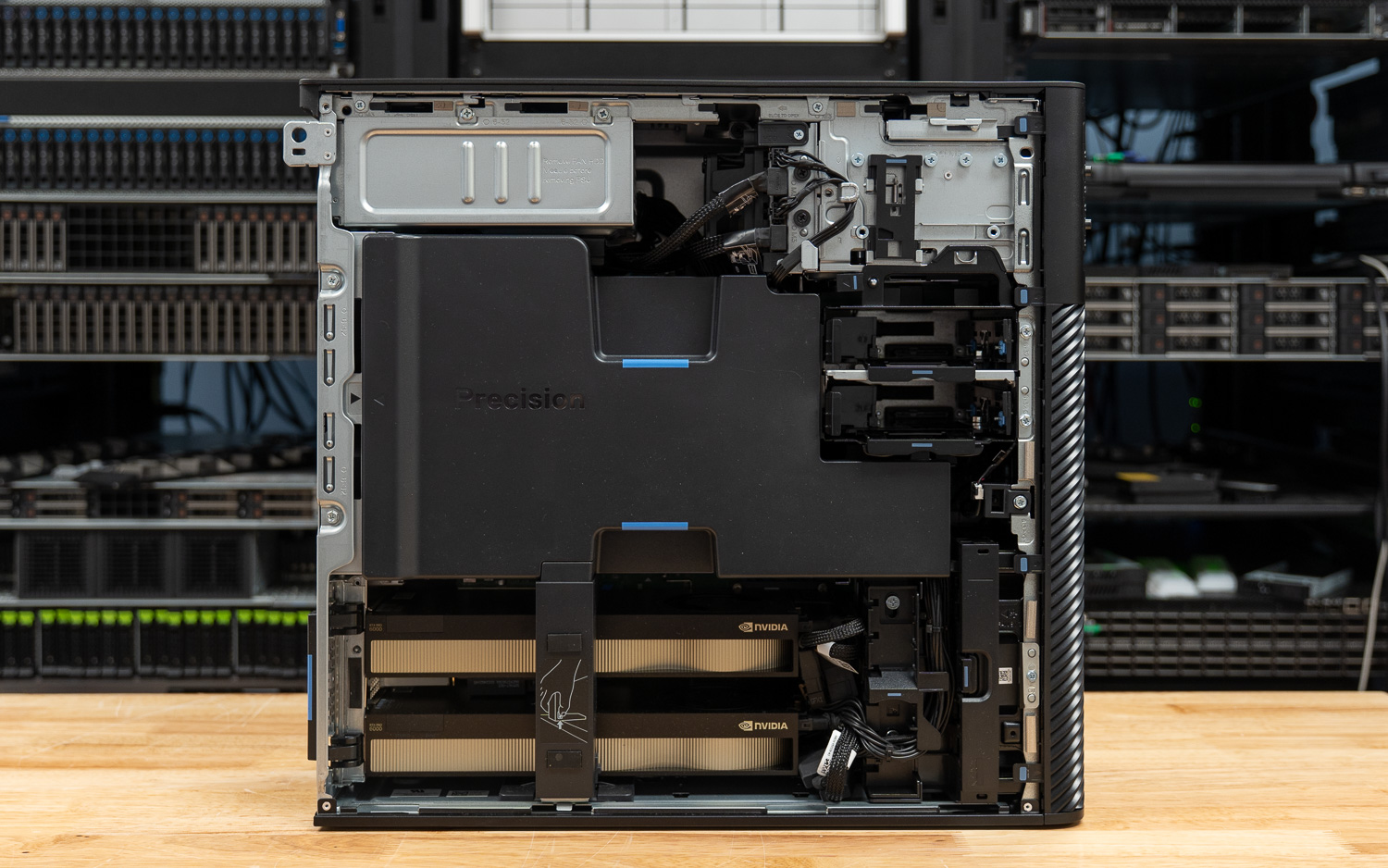
The Dell Precision 7875 combines the AMD Threadripper PRO 9995WX CPU with dual NVIDIA RTX PRO 6000 Blackwell GPUs,...

The expanded partnership will integrate Samsung's HBM4 memory with AMD's Instinct MI455X GPU, while also developing...

The Amazon Echo Spot, a compact smart speaker, sees its first price cut of the year at 38%, signaling a potential s...
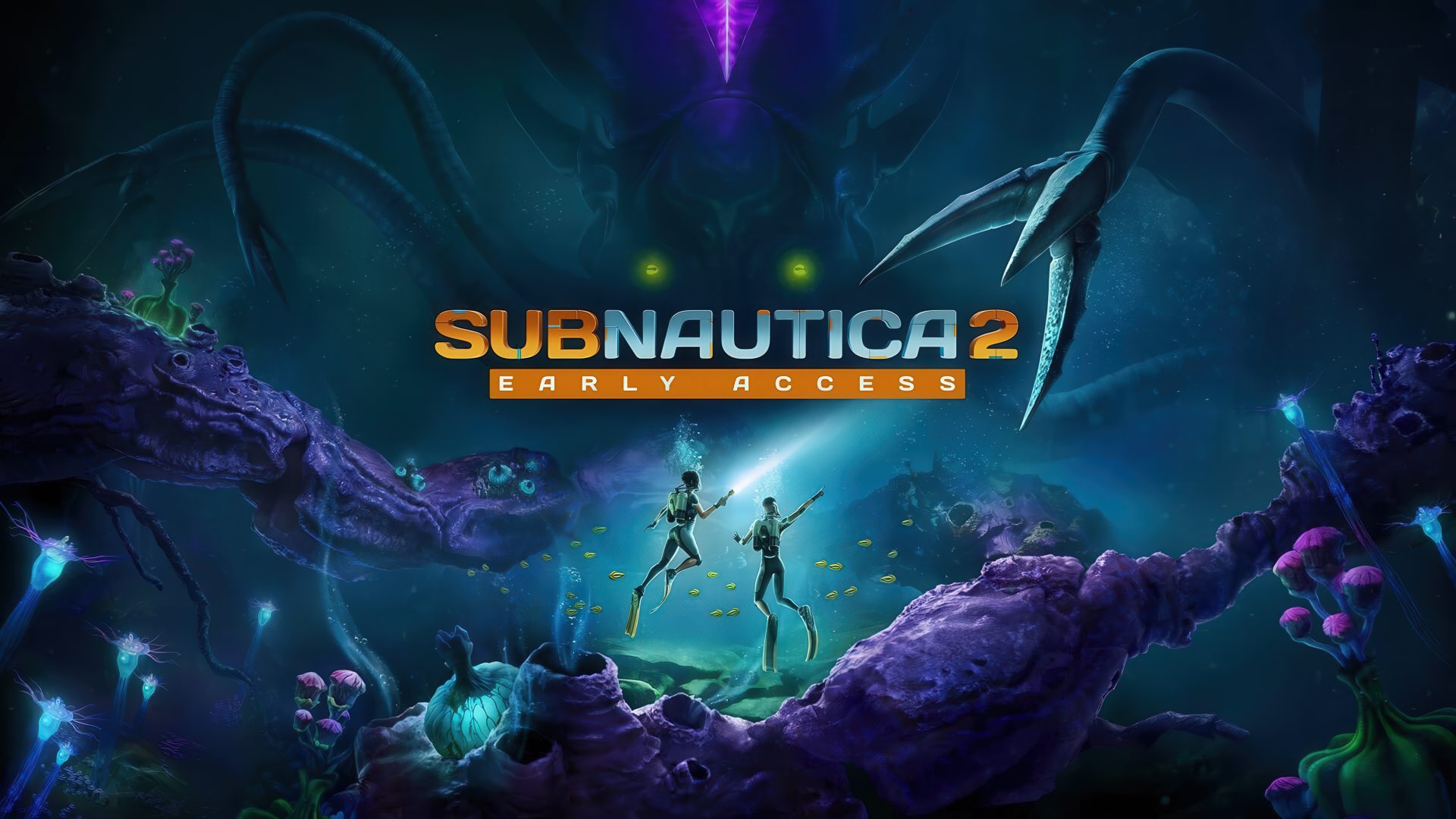
Subnautica 2 enters early access in May, marking the next chapter for Unknown Worlds' underwater adventure. New det...

The MacBook Neo's 8GB RAM configuration has faced criticism for being insufficient, but a recent stress test demons...

Ubiquiti's latest edge switch delivers 2.5G performance and PoE+ support at an accessible price, but practical limi...





