The Steam Controller is now available through official channels, eliminating scalper markups and ensuring developers get genuine hardware. Here’s what to know about its performance, value, and long-term potenti...










Blizzard’s ban on combat addons in *Midnight* isn’t just a technical limitation—it’s a deliberate push toward raids...

The Evolution Championship Series (EVO), a cornerstone of fighting game culture, has been acquired in full by Saudi...
A Reddit user’s MSI motherboard returned from RMA with an ASUS socket cover—damaging the pins—and now MSI is demand...
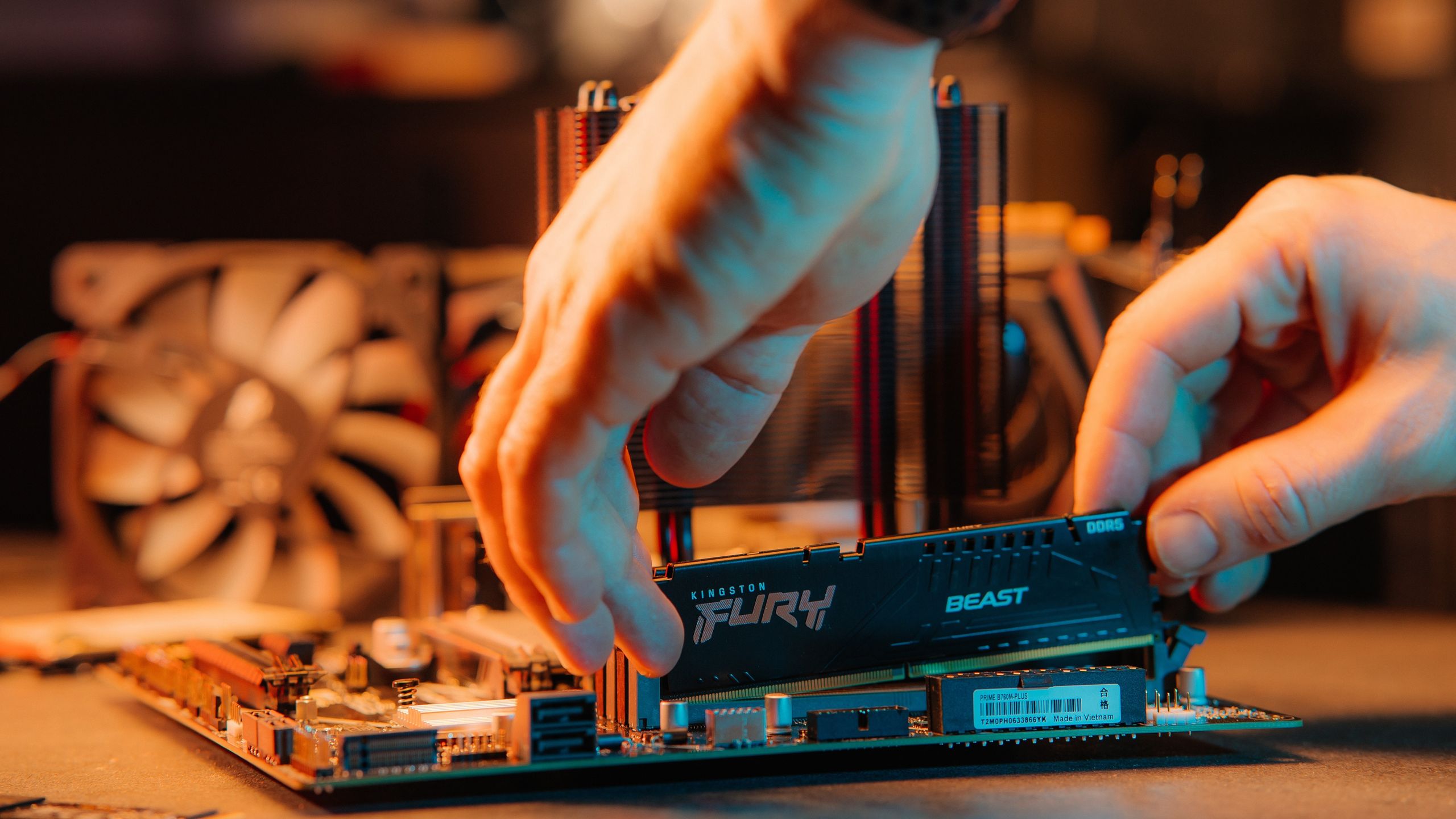
DDR5 shortages and DDR4 price surges have left PC builders desperate for affordable alternatives. Chinese manufactu...

With hard drive prices surging and new supplies scarce, a clever workaround emerges: repurposing used drives via do...

The upcoming Cosmetic Update for REPO is far more ambitious than just character customization, introducing gameplay...

After years of lagging behind TSMC, Samsung’s Pyeongtaek foundries are now running at near-full capacity, fueled by...

A new in-engine trailer for Forza Horizon 6 showcases Tokyo and beyond in stunning detail, with dynamic seasons, a...
ASRock Industrial has launched four new NUC mini-PCs designed for industrial and IoT applications, all powered by I...

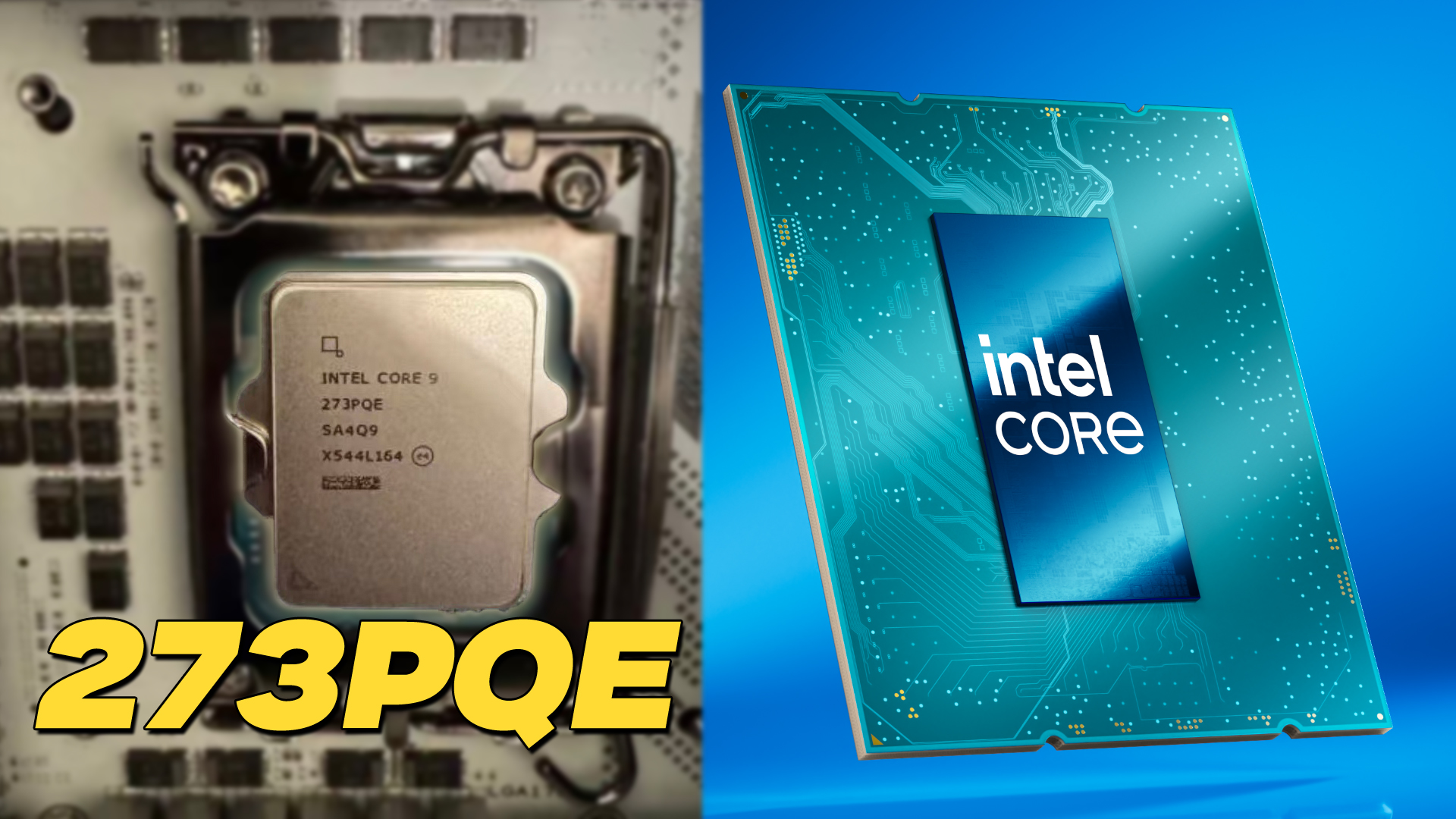
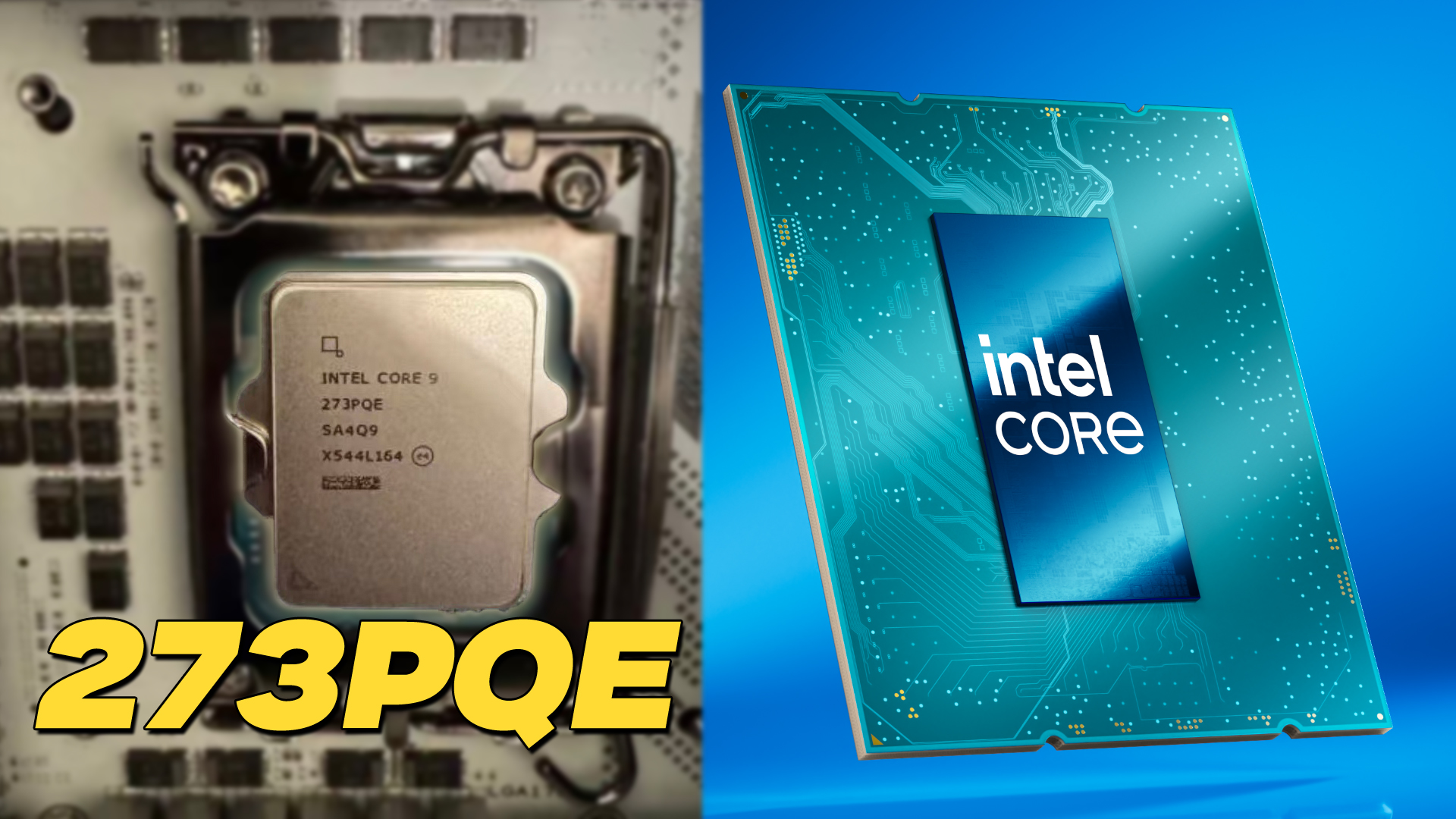
Intel is reassembling its engineering teams around a unified core architecture, effectively ending its long-standin...