Gigabyte’s new Z890 PLUS series targets enthusiasts seeking a balance of price and performance, offering up to 35% productivity gains over previous generations while introducing Ultra Turbo Mode for one-click B...








Meta’s AI ambitions just got a massive hardware boost. The partnership with NVIDIA isn’t just about scaling up—it’s...
A Gigabyte Aorus Master Ice RTX 5090 suffered connector melting despite extreme undervolting and a 500 W power limi...
The studio behind Demon’s Souls* and Shadow of the Colossus* will close in March, marking another major shift in So...

The upcoming Shrouded Sky update for *Arc Raiders* introduces hurricane conditions that reshape movement and combat...

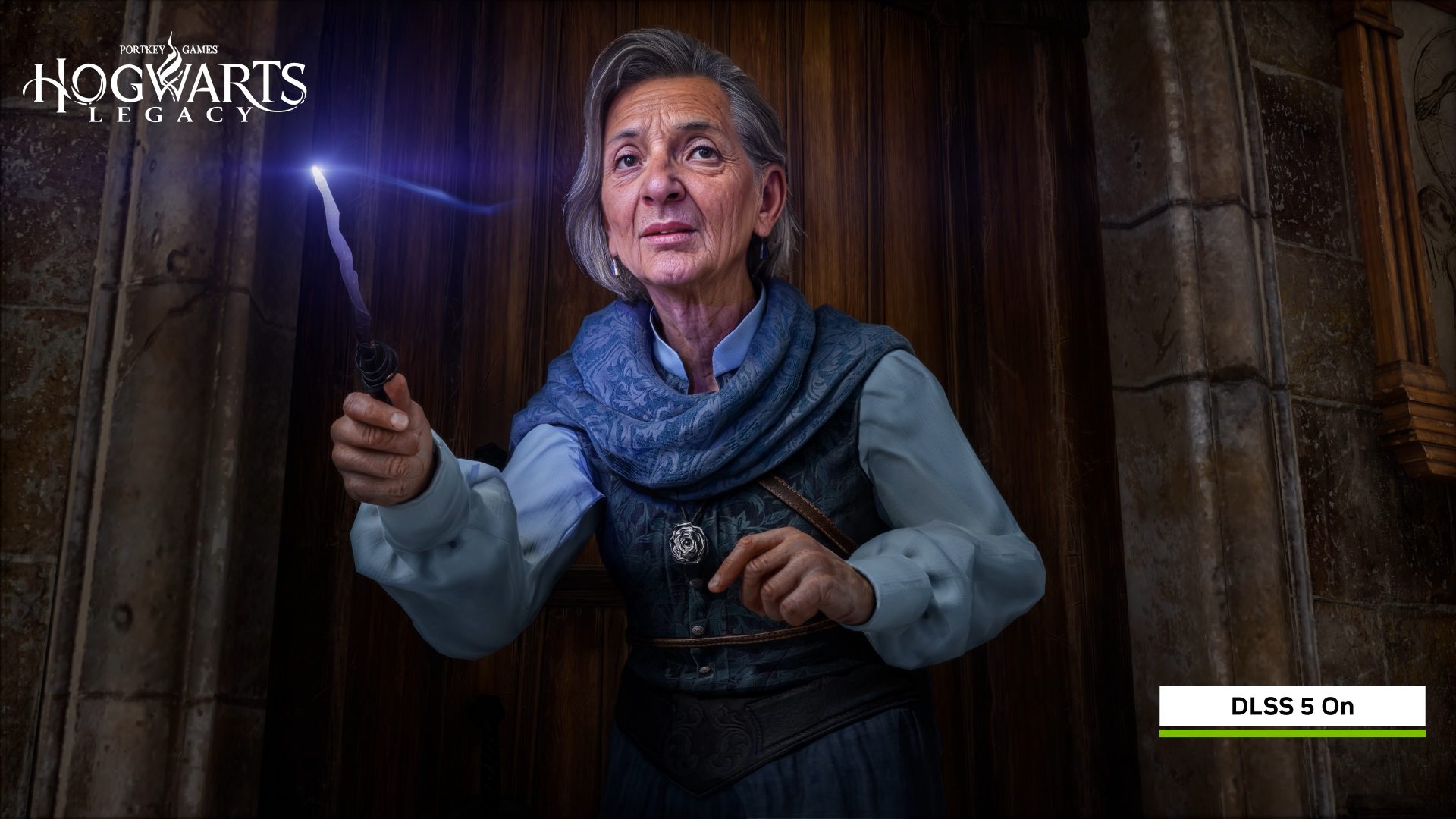
Generative AI is transforming NPCs into dynamic characters, but developers face an existential dilemma: How do you...

The Dutch defense secretary has suggested that European militaries could modify F-35 software independently—a move...

The movement behind the 1.3-million-signature EU petition against game destruction is formalizing its push with two...

Nerial’s Reigns: The Witcher* reimagines Geralt’s adventures through the lens of Dandelion’s storytelling, blending...

The developer behind Opus Magnum, a celebrated puzzle game, has unexpectedly revived its brand to release a new DLC...
Google’s latest AI architecture eliminates the need for multiple models by dynamically adjusting reasoning power—cu...