The Steam Controller, a device designed to bridge the gap between gaming and productivity, vanished almost instantly after its announcement. For creators who rely on dual-function hardware, this raises question...







AI systems now evolve faster than traditional compliance checks can keep up. The answer? Continuous auditing throug...

Lowiro’s upcoming title *In Falsus* blends high-profile composers, arcade-level precision, and PC accessibility—mak...

Stephen Kick, co-founder of Nightdive Studios, reveals how Dota 2* became a family tradition, a leadership school,...

After losing ground to SK hynix in late 2025, Samsung has surged back to the top of the DRAM market, driven by high...

A standalone prequel for Trench Foot—a *Doom 2* mod blending World War I trench combat with medieval fanaticism—has...

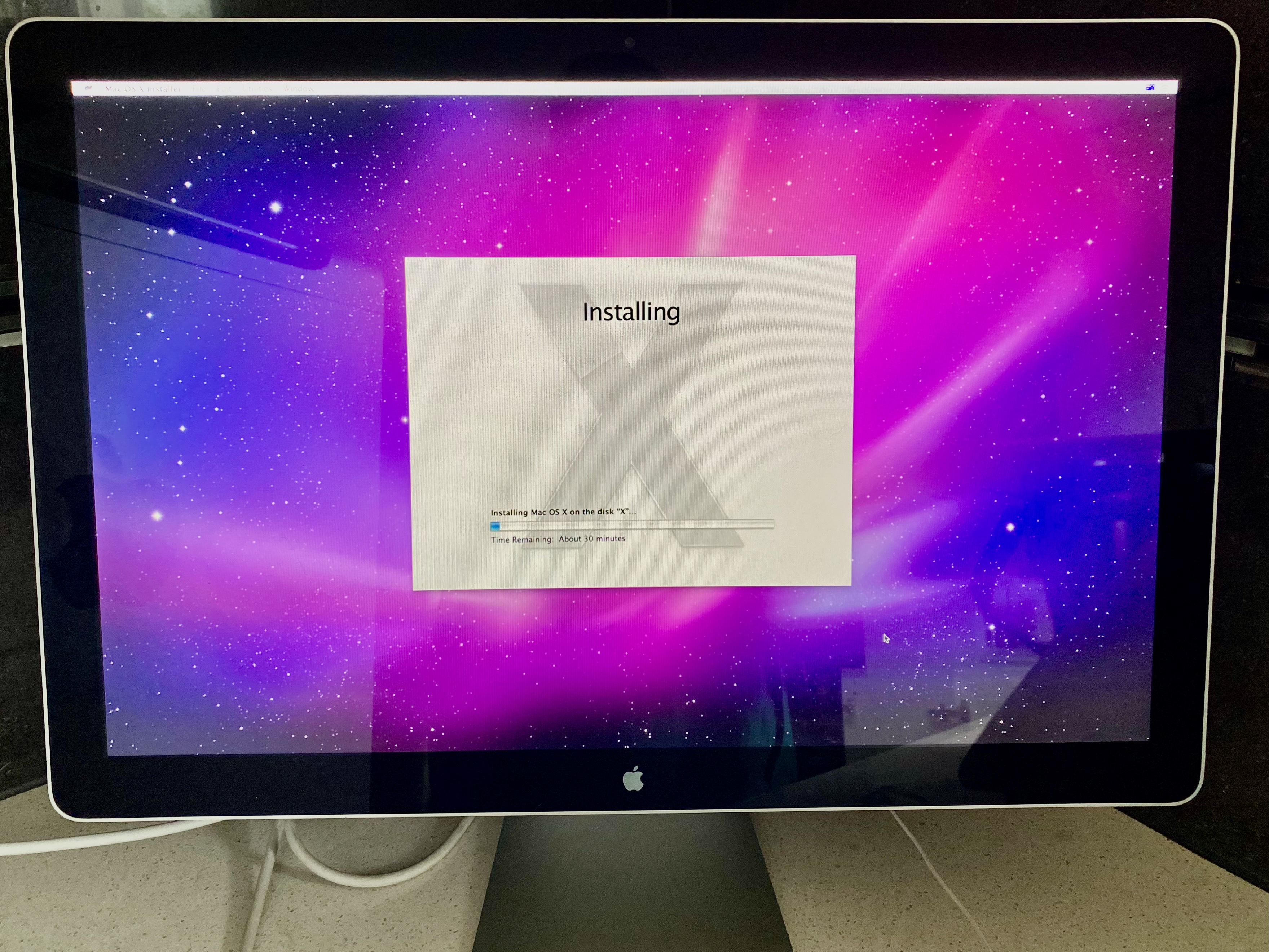
Apple’s retail shelves are emptying faster than expected, with multiple models—from the iPhone 16e to the M4 MacBoo...
The UK’s Online Safety Act now requires platforms like Discord, Reddit, and Xbox to enforce age checks, but the met...

Twice Circled’s aquarium management sim receives a sweeping free update alongside its upcoming *Invertebrilliant Co...

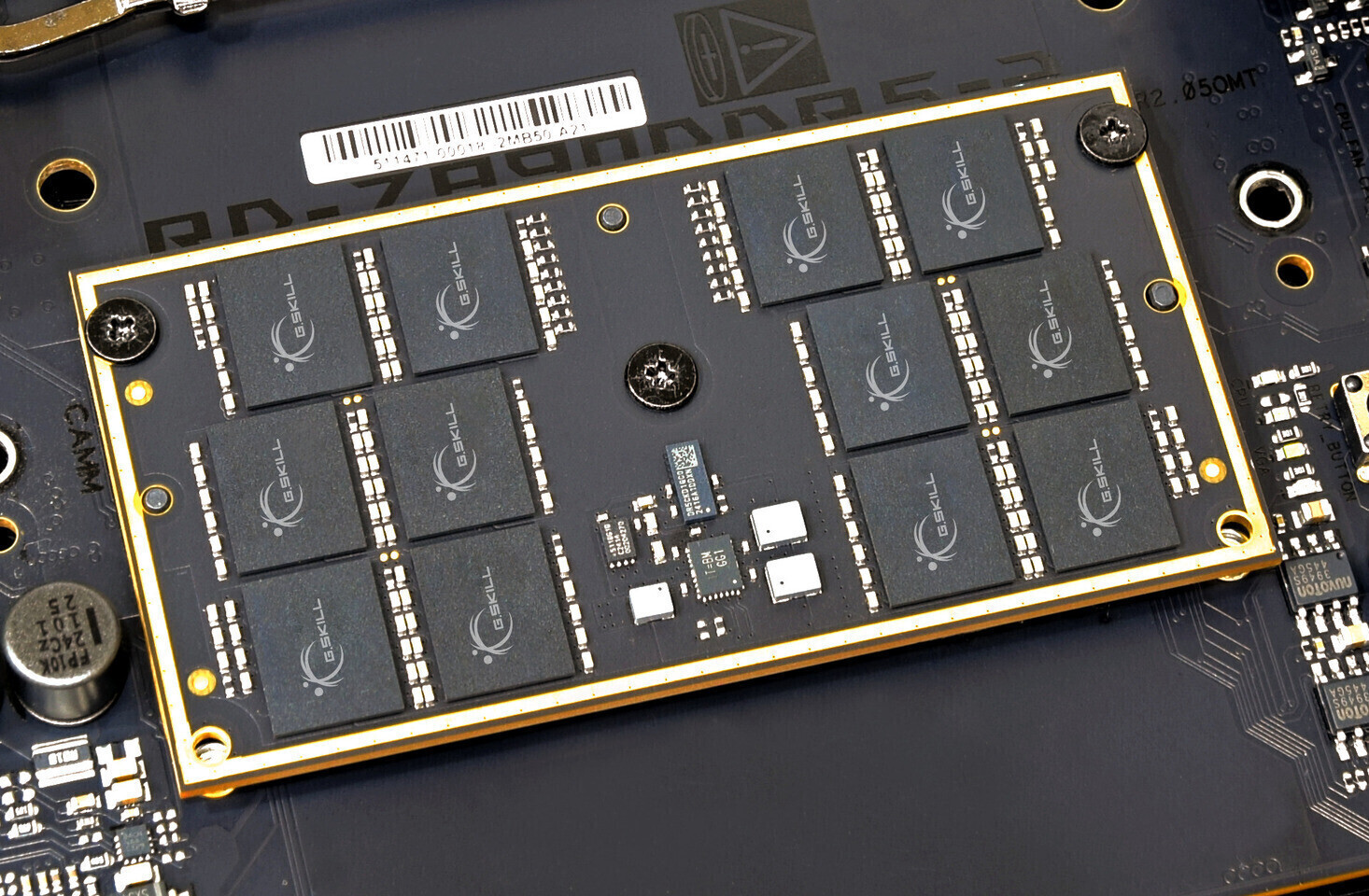
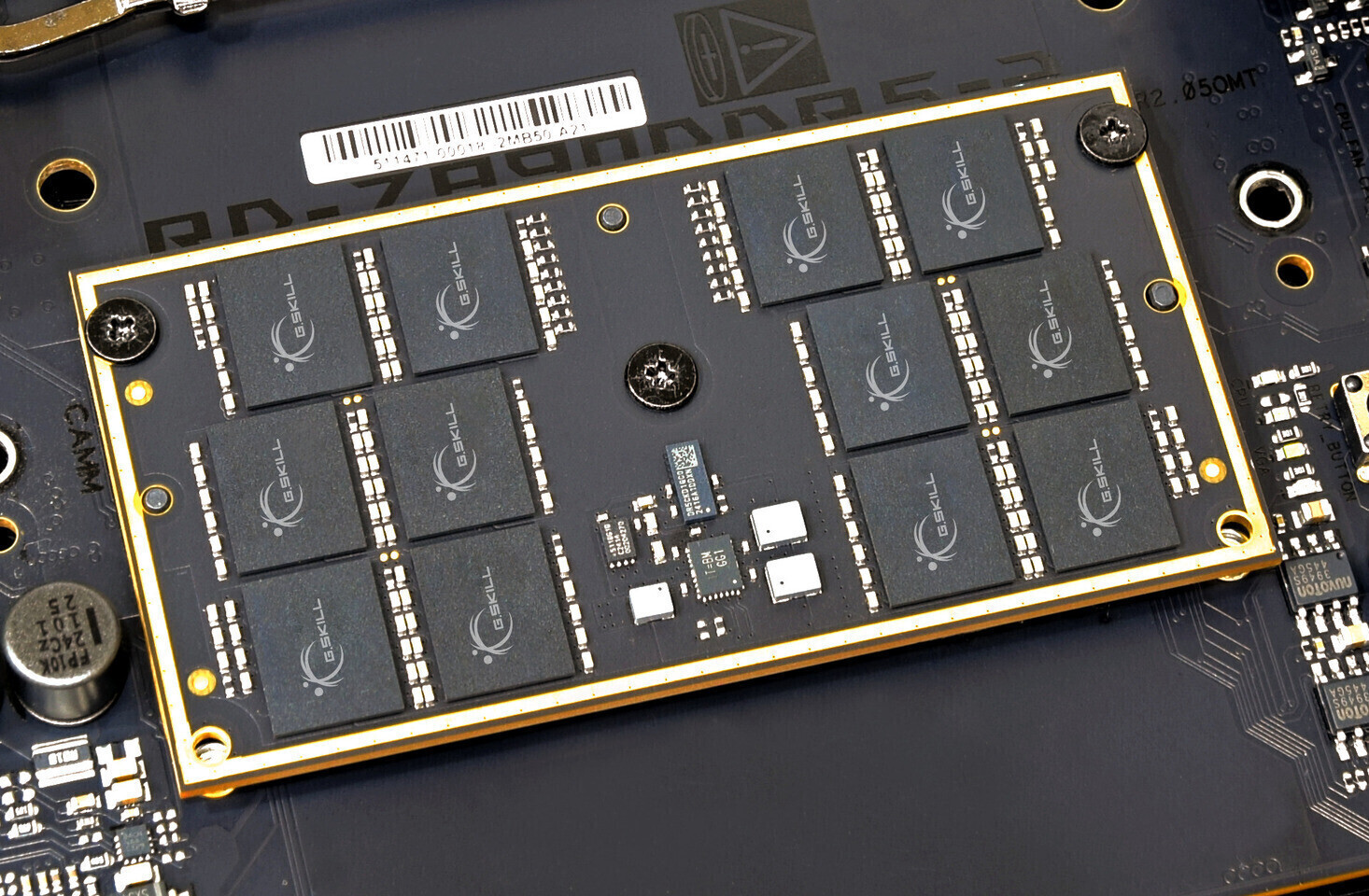
Lenovo’s final warning to resellers has sent shockwaves through the tech supply chain. A 32GB DDR5 kit—already pric...

Trigger Happy Interactive’s *Total Chaos* remake is getting a terrifying New Game+ mode that introduces a persisten...