NVIDIA's latest open-source model, Nemotron-3-Super, has surpassed competitors in performance metrics, influencing upgrade decisions for developers and researchers.









Sapphire’s limited-edition NITRO+ Radeon RX 9070 XT OC Crimson Desert Edition has surfaced in European stockists, r...

Nexon’s Q4 financials reveal a dramatic revenue surge, driven largely by ARC Raiders—the extraction shooter that ha...

Samsung Display has formalized its latest QD-OLED innovation—a five-layer organic light-emitting structure—under th...

Netflix, Disney+, and Peacock automatically drain gift card balances after cancellation, leaving users with no way...
The latest Chrome version integrates payment and address data from Google Wallet while addressing critical vulnerab...

Best Buy’s latest GPU pricing fiasco—listing an RTX 5090 for $5,090—exposes a broken market where hardware costs de...

Lenovo’s Q3 2025 results show a 18% revenue surge, with AI revenue now accounting for 32% of total earnings. Strate...
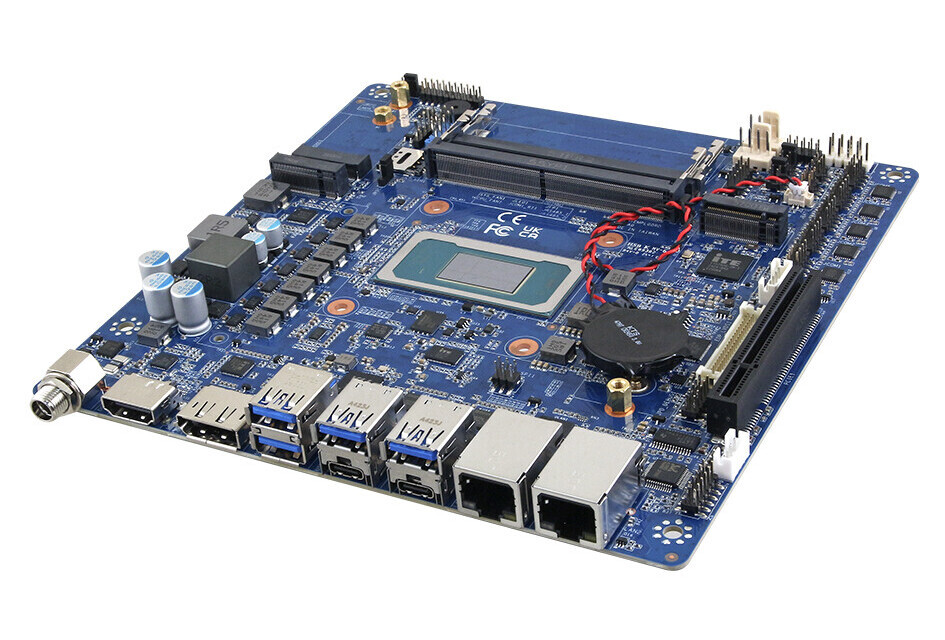
Avalue’s new EMX-PTLP Mini-ITX board supports Intel’s latest Core Ultra H-series chips, DDR5-7200 memory, and PCIe...
NVIDIA’s cloud gaming service has just unlocked Amazon Fire TV devices, adding a new way to turn any TV into a high...

Qualcomm’s Snapdragon X2 Elite delivers a dramatic performance leap over its predecessor, but Apple’s M5 remains th...