Rockstar Games is adopting a console-first strategy for its next-generation titles, including the highly anticipated GTA 6. This shift reflects broader industry trends where hardware optimization and platform e...







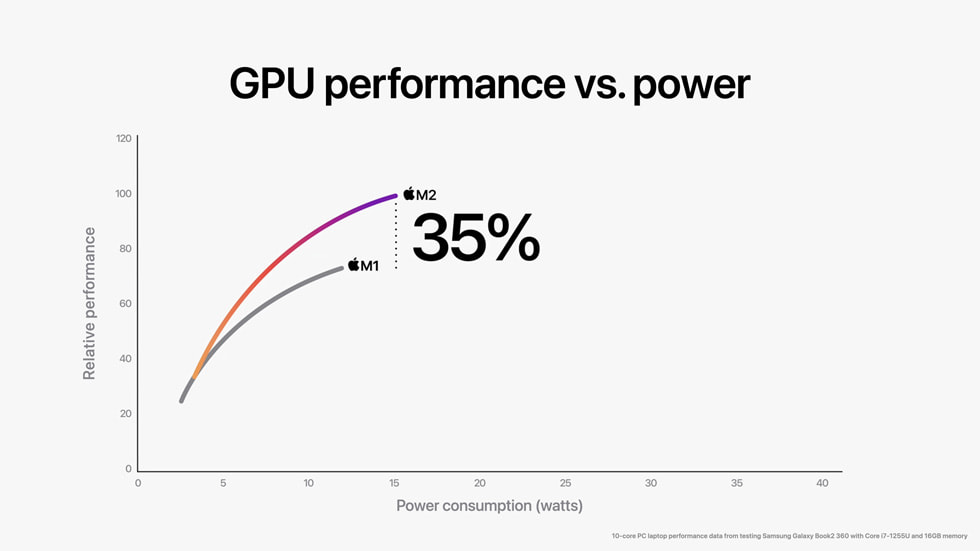
Apple’s upcoming product wave hints at a rare flurry of innovation—from a budget-friendly MacBook to high-refresh S...

After months of speculation about a radical AI companion device, OpenAI’s first hardware may be a familiar form fac...
A removed Microsoft blog post from late 2024 demonstrated training an Azure AI system on pirated copies of J.K. Row...

A limited-edition *Resident Evil Requiem* bundle featuring a pull-up bar sold out in hours, blending workout gear w...

The publisher’s CEO outlines a bold expansion of its two biggest franchises—including a return to multiplayer for A...
For streamers and content creators, choosing between PCIe and USB capture cards often hinges on resolution, platfor...

The voice of Geralt of Rivia reveals his first-time playthrough experience, favorite locations, and the quest that...

NVIDIA’s latest commitment to OpenAI has been scaled back dramatically, with the tech giant finalizing a $30 billio...
Swiss researchers uncovered critical vulnerabilities in Bitwarden, LastPass, and Dashlane, exposing risks to encryp...
A new Teams feature will automatically log employees’ office locations via Wi-Fi, raising questions about workplace...