

The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...









The upcoming 1.7 update for Stardew Valley introduces two new marriage candidates, but one in particular, Clint, ha...

The latest flagship chip from Samsung, the Exynos 2600, has made significant strides in thermal performance, addres...

A lean, dual-narrative design proves that survival horror can be both concise and complete, delivering a full exper...
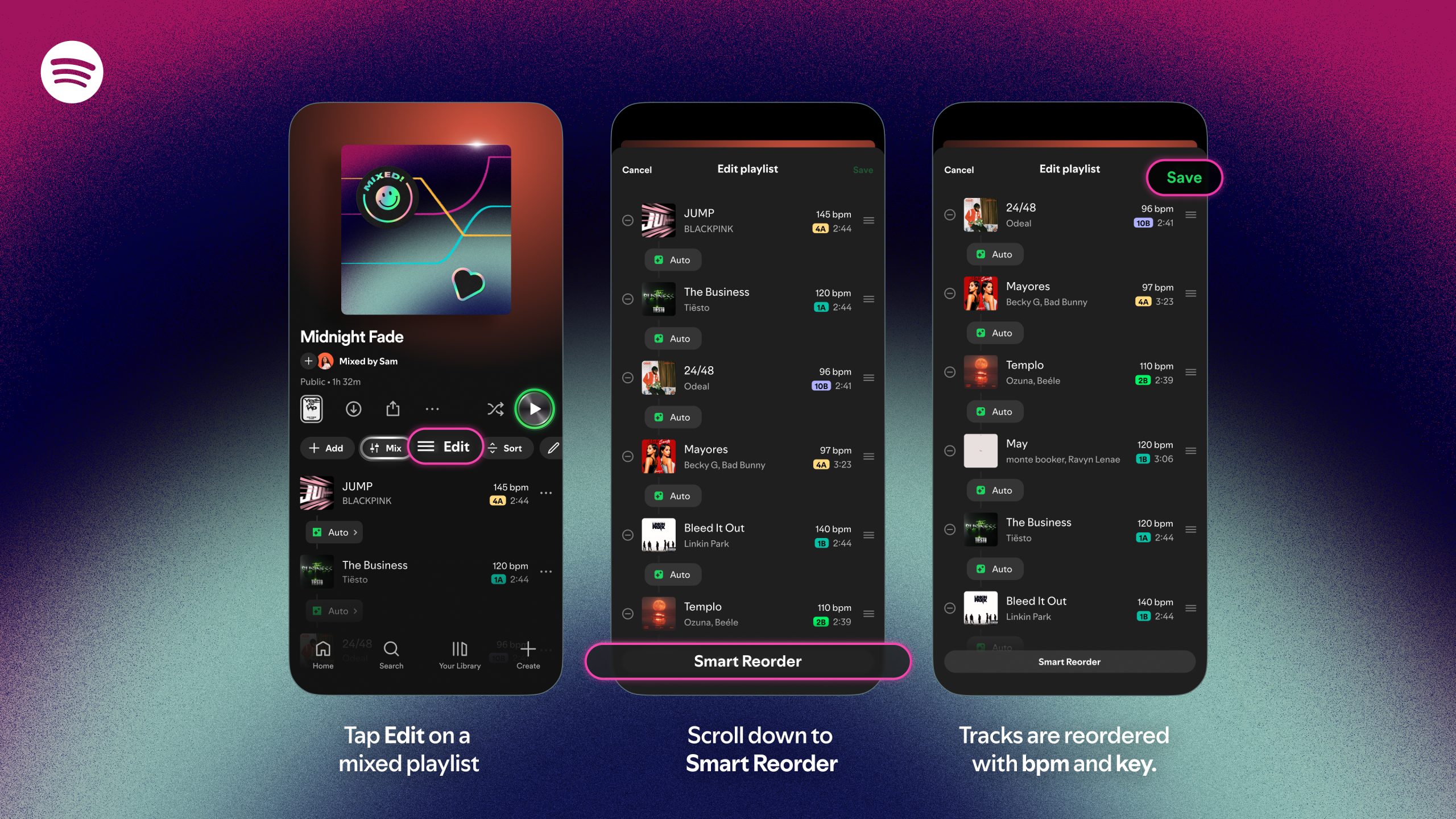
Premium users can now automatically sort playlists by BPM and key, creating smoother transitions between songs. The...

A new roguelike game, Bingo Betty, combines the addictive mechanics of bingo with procedural generation, offering a...

The Acer Swift Go 14 delivers a balance of performance, portability, and value, making it an attractive option for...
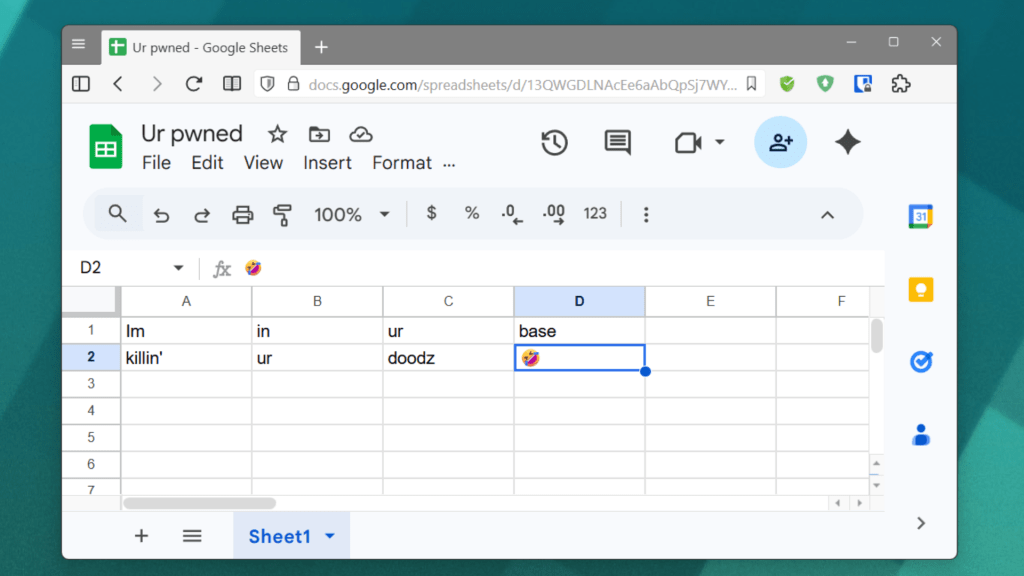
A China-linked hacking group exploited Google Sheets to spy on global targets, highlighting the risks of everyday s...

Price hikes for the Steam Deck OLED in Asia may signal a new phase for Valve’s handheld, but whether they’ll ripple...

A new outlet extender from Addtam offers a practical way to expand charging capacity without clutter, featuring nin...
A new multi-year collaboration will integrate OpenAI's advanced models with AWS infrastructure, focusing on statefu...





