Rockstar Games is adopting a console-first strategy for its next-generation titles, including the highly anticipated GTA 6. This shift reflects broader industry trends where hardware optimization and platform e...





A 5-fold increase in memory prices and a 3-fold rise in storage costs since early 2025 are expected to squeeze vend...
The Intel Arc Pro B70 quad-GPU system delivers impressive performance for AI inference tasks, but its high power co...

Dell anticipates a surge in AI-driven memory demand that could reshape PC building and enterprise storage strategie...

A new graphics processing unit from AMD is tailored specifically for data workloads, featuring optimized memory and...

The EIZO ColorEdge CS3200X introduces a 31.5-inch 4K display with advanced color management, HDR support, and USB-C...

AI tools now handle complex edits automatically, but the best results still require human oversight to avoid over-p...

A new compact gaming keyboard leverages Tunnel Magnetoresistance (TMR) and 8000 Hz polling to redefine input precis...

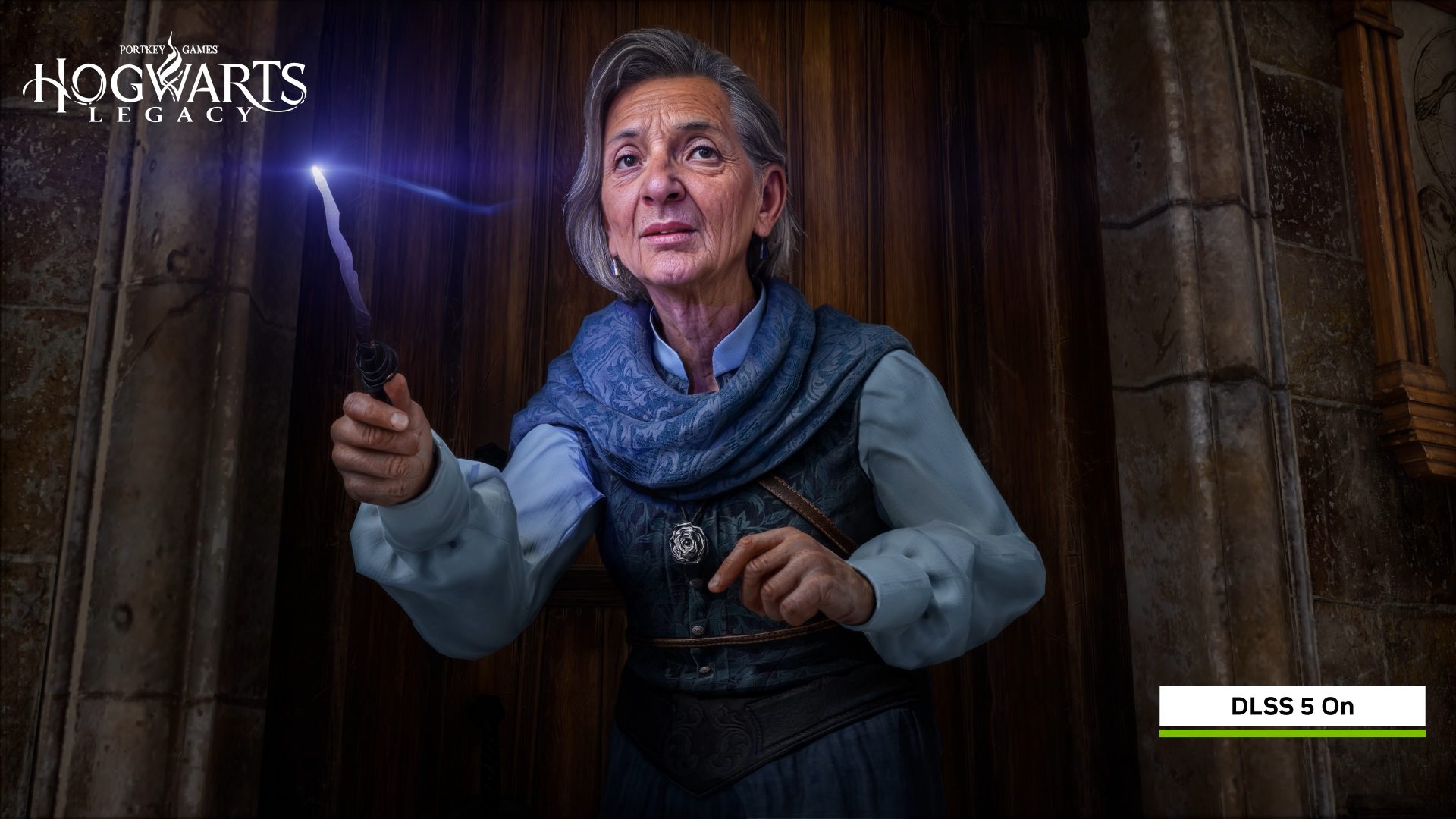
The Nintendo Switch 2’s improved CPU and GPU architecture suggests deeper integration of DLSS-like upscaling, but r...

The new Thermalright AI HydroNous R1 mini PC leverages a water-cooled Ryzen AI Max+ 395 processor, targeting AI wor...

Rockstar Games is set to transform player earnings in GTA 6 with a user-generated content model that could generate...