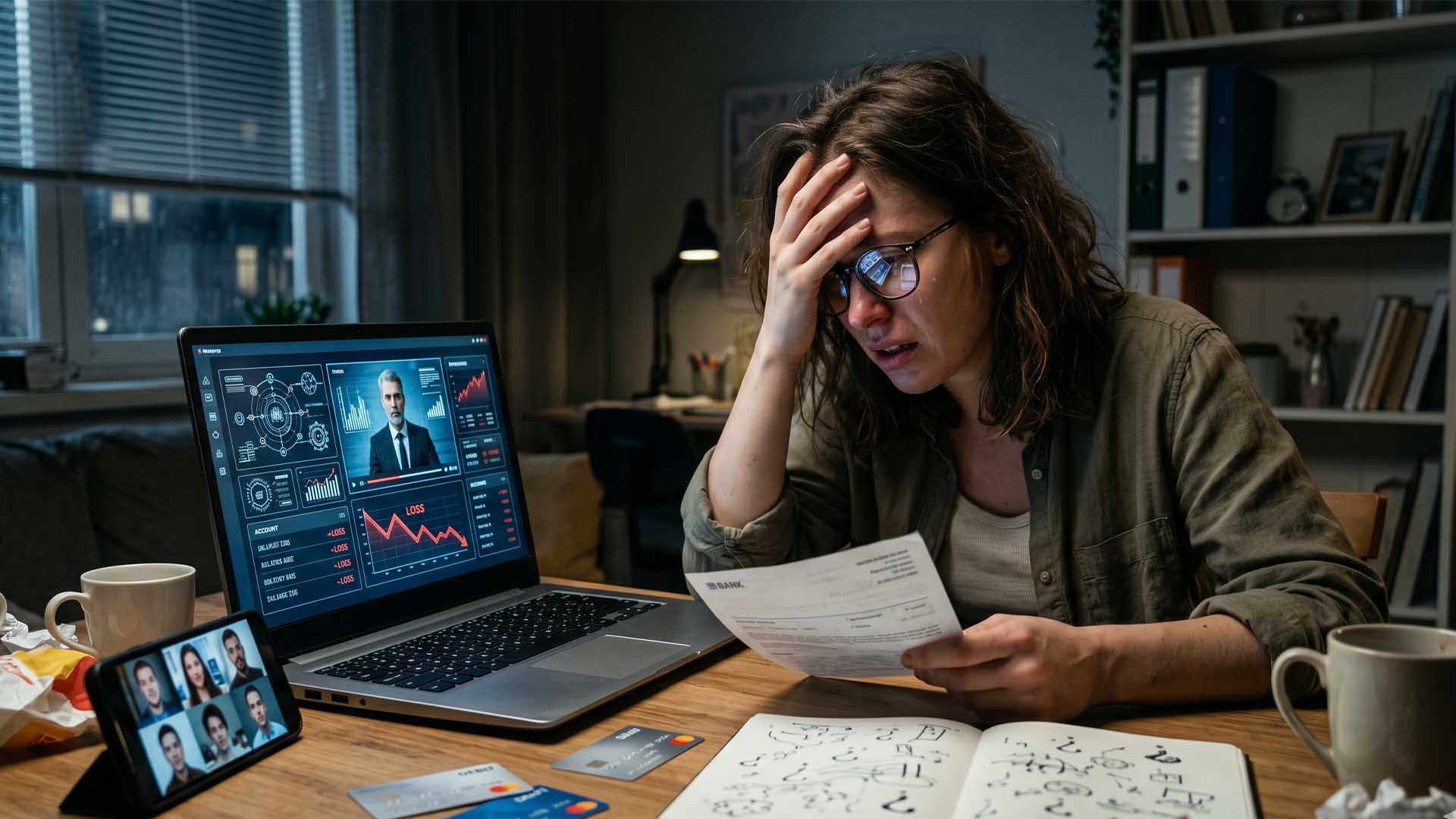
Imagine a vault containing 6 billion keys—each one a password stolen from real users over the past year. The contents aren’t random. They’re predictable, repetitive, and shockingly weak. Researchers analyzing this trove of compromised credentials found that the most stolen passwords aren’t just 'password' or '123456'—they’re variations of these themes, often stretched to eight characters just to meet minimum requirements. The result? A digital landscape where even slightly modified guesses can unlock accounts, exposing everything from personal emails to corporate systems.
The data, compiled by security firm Specops Software, paints a grim picture of modern password habits. The top five most stolen credentials remain unchanged from years past: '123456', '123456789', '12345678', 'admin', and 'password'. But the problem runs deeper. Users aren’t just recycling these defaults—they’re appending predictable suffixes like '@123' or combining them with generic terms ('hello@123', 'welcome123'). The keyboard shortcut 'qwerty' still ranks highly, as do passwords tied to common roles ('student', 'guest'). Worse, nearly one in six passwords in the dataset hit the arbitrary eight-character mark—not because users are suddenly inventive, but because platforms enforce it as a baseline.
The scale of the threat is staggering. Five malware families—LummaC2, RedLine, Vidar, StealC, and Raccoon Stealer—accounted for nearly 100 million stolen credentials in 2025 alone. LummaC2 alone swiped over 60 million passwords, making it the most prolific. These tools don’t just target individuals; they’re often bundled with other malicious software, turning phishing campaigns into high-volume credential harvesters. Less tech-savvy users are particularly vulnerable, as they’re more likely to fall for deceptive emails or fake login prompts.
So what’s the fix? Security experts emphasize that complexity alone isn’t enough. A password like 'P@ssw0rd!' might meet requirements, but it’s still a derivative of 'password' and just as guessable. The real defenses lie in three strategies
- Password managers: Tools like Bitwarden, 1Password, or KeePass generate and store unique, random passwords for every account, eliminating the need to remember—or reuse—anything predictable.
- Two-factor authentication (2FA): Even if a password is stolen, a second layer—like a code from an authenticator app or a hardware key—adds a critical barrier. Platforms from Apple to Google now make 2FA the default for sensitive accounts.
- Leak checks: Services like Have I Been Pwned allow users to verify if their email or password has appeared in known breaches. If it has, it’s time to change it—immediately.
For organizations, the stakes are even higher. Admins should enforce regular password rotations (every 6–12 months) and ban common patterns entirely. The days of 'admin' or 'welcome123' as defaults are over—not because users are getting smarter, but because attackers are.
The irony is that the solution isn’t more complicated passwords. It’s recognizing that passwords, by design, are flawed. The real security lies in layers: managers to create strength, 2FA to add depth, and vigilance to spot threats before they strike. The 6 billion stolen credentials aren’t just a warning—they’re a wake-up call. The question is whether users will finally listen.