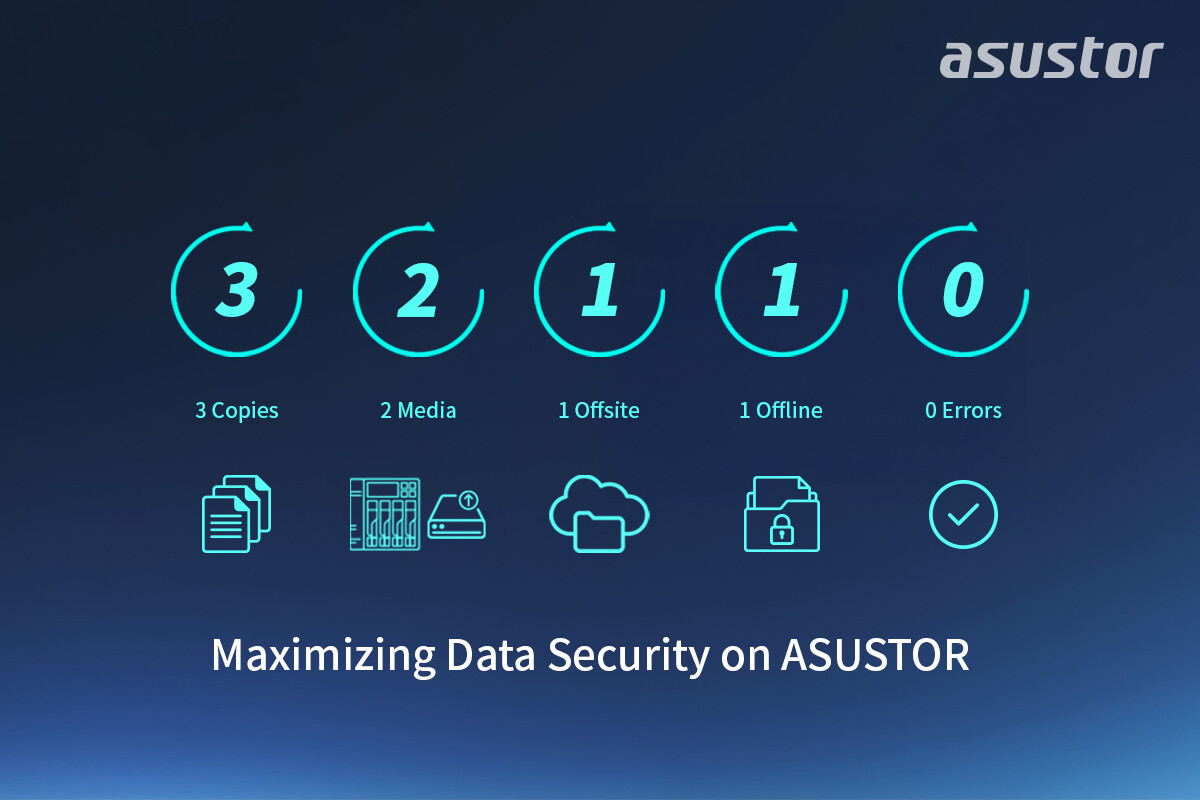
Enterprises are no longer just backing up data—they’re fortifying it against an evolving threat landscape where ransomware can leap from one drive to another with alarming speed. The traditional 3-2-1 backup rule—three copies, two media types, one offsite—has been the gold standard for decades. But as attack vectors grow more sophisticated, a stricter variant is emerging: 3-2-1-1-0.
This updated protocol doesn’t just add redundancy; it demands that one copy remain physically isolated and immutable while requiring every backup to be verified with zero errors. The shift isn’t minor—it’s a fundamental rethinking of how data resilience is engineered, especially in network-attached storage (NAS) systems.
Hardware Meets the New Protocol
The 3-2-1-1-0 standard places heavy demands on both hardware and software. To meet those demands, a major NAS manufacturer has introduced features that address each layer of the protocol
- RAID 50 and RAID 60 support: These configurations allow for dual-parity protection, ensuring data remains intact even if multiple drives fail simultaneously.
- WORM (Write Once, Read Many) technology: Once data is written in WORM mode, it cannot be altered or deleted—even by administrators. This creates an impenetrable barrier against unauthorized changes.
- Post-Quantum Cryptography (PQC) readiness: The manufacturer is the first NAS provider to integrate PQC algorithms, preparing for a future where quantum computing could break traditional encryption.
- MyArchive for offline isolation: This feature allows hard drives to be physically removed and stored as removable media, creating an air gap that ransomware cannot penetrate.
The hardware underpinning this protocol isn’t just about adding layers—it’s about ensuring those layers are both performant and resilient. The Lockerstor R Pro Gen2 series, for example, is designed to handle extreme data transfer scenarios while maintaining security. But performance comes with tradeoffs: dual-parity RAID configurations like RAID 50 and RAID 60 improve protection but can impact write speeds in high-load environments.
Software as the First Line of Defense
While hardware provides the foundation, software is where the protocol truly takes shape. The Snapshot Center, built on Btrfs, enables fast, space-efficient virtual snapshots. In the event of ransomware or accidental deletion, users can restore data to a previous state without needing offline media—though offline backups remain critical for the highest level of protection.
ADM (ASUSTOR Data Management) ties these features together, offering a unified interface where enterprises can configure WORM policies, verify backups, and manage snapshots. The integration is deep enough that even smaller businesses can implement enterprise-grade defenses without prohibitive costs—a departure from the past, where such resilience was reserved for large organizations.
That’s the upside—here’s the catch: implementing 3-2-1-1-0 isn’t just about buying new hardware. It requires a shift in workflow, especially around offline storage and verification processes. For businesses that treat backups as a set-and-forget operation, this protocol will demand discipline.
The question isn’t whether the 3-2-1-1-0 standard is necessary—it’s whether enterprises are ready to adopt it before ransomware evolves further. Pricing and availability for systems supporting this protocol have not been confirmed, but the trend suggests a move toward stricter security frameworks that balance cost with resilience.