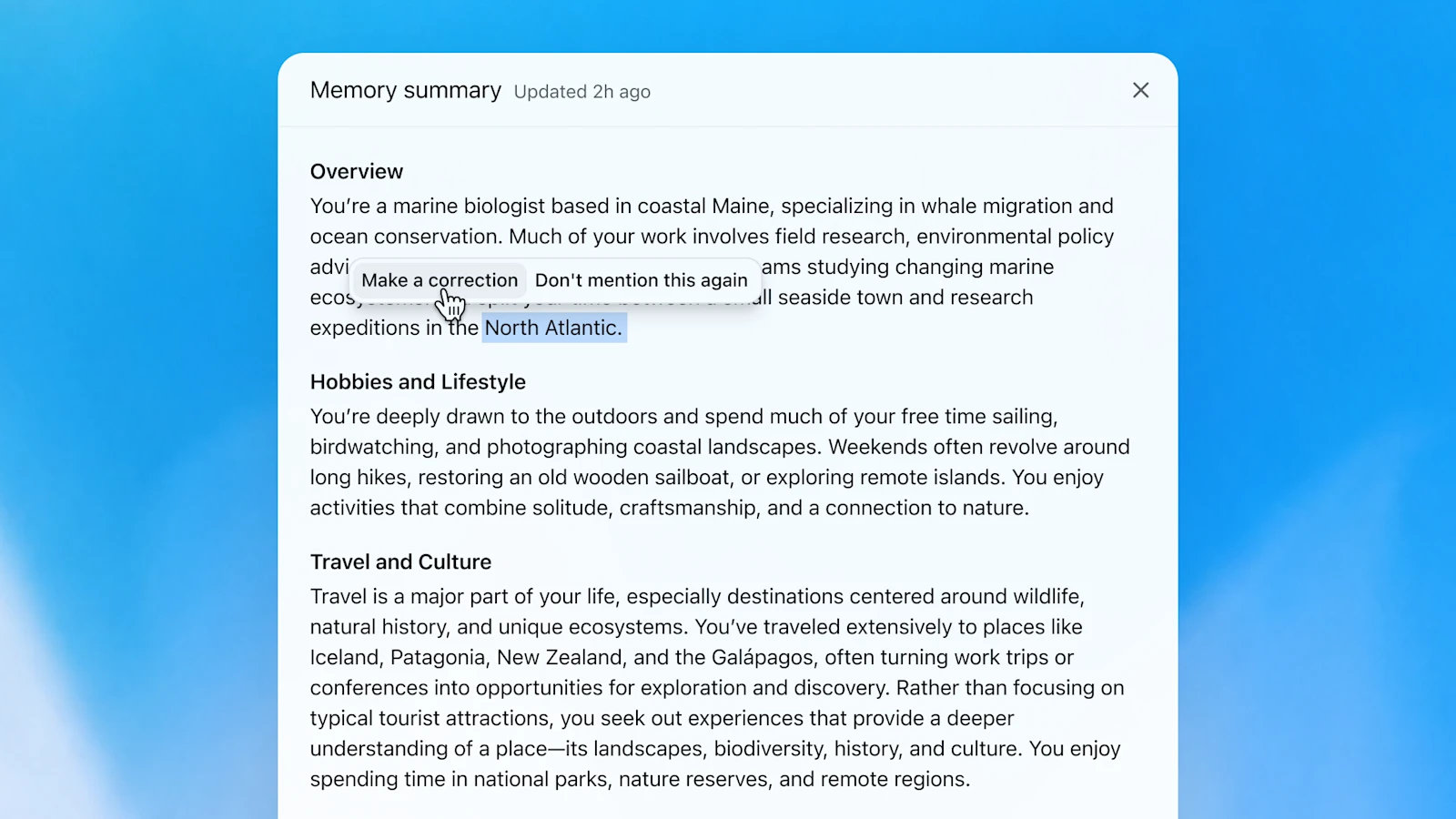
Cybercriminals are increasingly employing a refined phishing technique known as browser-in-the-browser (BITB) attacks to steal Facebook login credentials. This method creates a convincing fake browser window, complete with authentic-looking URLs and interface elements, making it difficult for users to distinguish between real and fraudulent pages.
Unlike traditional phishing attempts that rely solely on spoofed web addresses, BITB attacks generate an entire simulated browser environment. This includes a functional address bar displaying a legitimate domain, which can mislead even cautious users. The attack typically begins with unsolicited messages—emails or texts—urging recipients to verify their accounts due to alleged security concerns.
Once lured to the fake page, victims encounter additional layers of deception, such as CAPTCHA prompts, which further lower suspicions before presenting a fraudulent login form. Facebook’s vast user base, exceeding two billion active daily users, amplifies the risk, particularly among less tech-savvy individuals who may be more susceptible to such tactics.
Security researchers have observed a notable increase in these attacks, highlighting their effectiveness in bypassing conventional security checks. Users can attempt to identify BITB attacks by testing interactions within the fake browser window—such as dragging its title bar—which often proves impossible with genuine browser behavior.
The best defense remains skepticism and verification. Logging into Facebook through a separate browser or device, rather than following unsolicited links, provides an immediate way to confirm authenticity. While no platform is immune to evolving threats, awareness of these techniques can significantly reduce exposure for users across all digital services.